Getting Started Guide
Document Version: 1.0 – 2021-04-15
CUSTOMER
Getting Started with the
SAP S/4HANA 2020 (FPS01) Fully-Activated Appliance
Table of Contents
1 Solution Information ..................................................................................................................... 4
Introduction ............................................................................................................................................................. 4
Installed Products.............................................................................................................................................. 5
Business Scenarios & Localizations ................................................................................................................ 6
ABAP client structure & business users .......................................................................................................... 8
Sample Demo Walkthroughs ............................................................................................................................ 9
Recommended Post-Installation Steps ........................................................................................................... 9
More Information & Support ............................................................................................................................ 9
1.7.1 More Information .......................................................................................................................................... 9
1.7.2 Support ......................................................................................................................................................... 10
2 Accessing the Solution ................................................................................................................ 11
Overview ............................................................................................................................................................ 11
Option 1: System access via embedded Windows Remote Desktop frontend server ............................... 11
Option 2: System access via local PC ............................................................................................................. 13
2.3.1 Mapping your local
/etc/hosts
file ............................................................................................................. 13
Users & passwords for the system components........................................................................................... 14
2.4.1 SAP S/4HANA ABAP application server ................................................................................................... 14
2.4.1.1 Pre-configured business users in SAP S/4HANA ................................................................................ 14
2.4.1.2 Administrative data & users for SAP S/4HANA ................................................................................... 15
2.4.2 SAP HANA DB server ................................................................................................................................... 16
2.4.3 Java Application Server ............................................................................................................................... 17
2.4.4 SAP BusinessObjects BI platform .............................................................................................................. 18
2.4.5 Windows Frontend Server Details .............................................................................................................. 18
2.4.6 Accessing Your Instance on Linux Level .................................................................................................... 19
Optional: Get your own fully-qualified domain name & SSL certificate ...................................................... 19
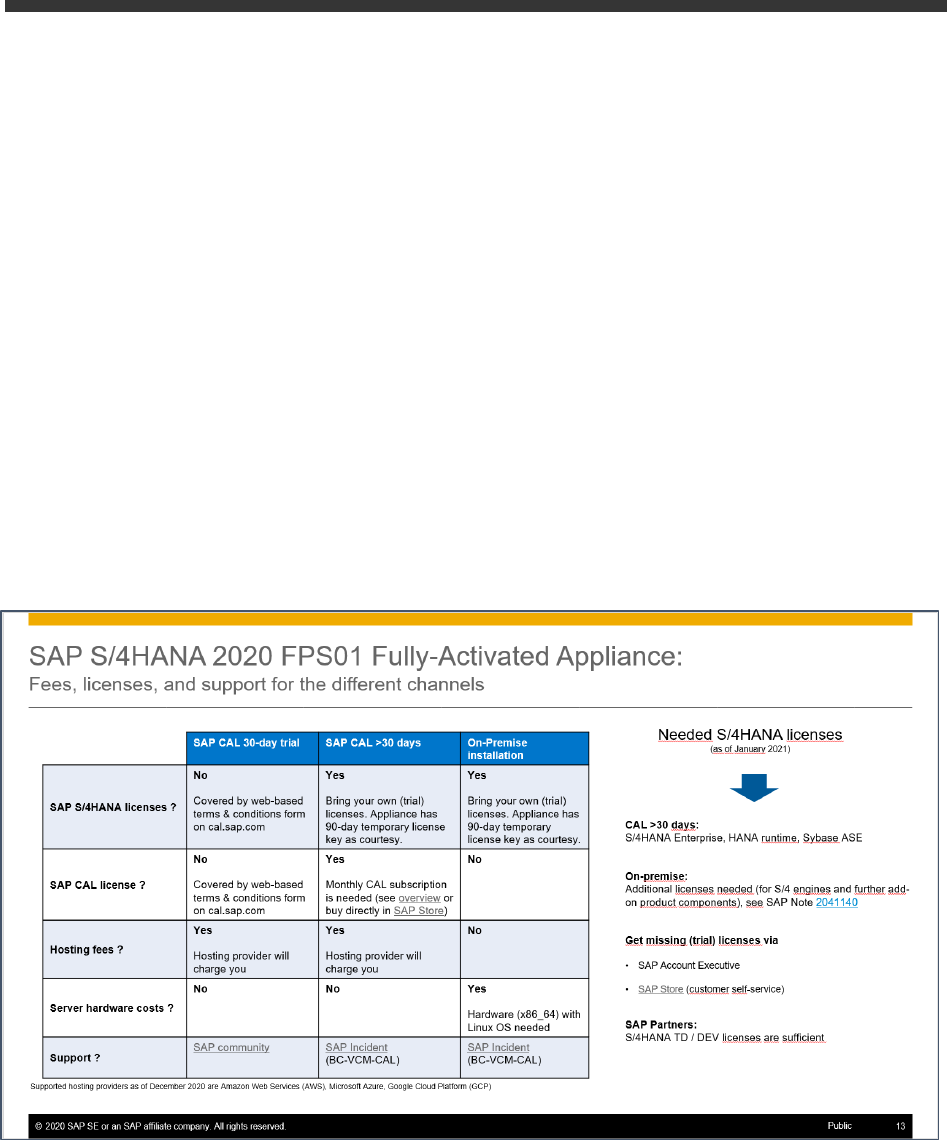
3 Licenses & Fees .......................................................................................................................... 20
First 30 days: Running your system instance as trial ................................................................................... 21
Beyond 30 days: Running your instance with SAP licenses ......................................................................... 21
3.2.1 SAP CAL subscription ................................................................................................................................. 21
3.2.2 SAP product licenses .................................................................................................................................. 22
3.2.2.1 SAP S/4HANA Enterprise Mgmt. & SAP HANA DB ............................................................................ 22
3
3.2.2.2 Optional: SAP BusinessObjects BI Platform licenses .................................................................... 22
Beyond 90 days: License key installation required ...................................................................................... 23
3.3.1 What to do if your temporary license key has expired ............................................................................ 24
4 Security Aspects in SAP CAL ..................................................................................................... 25
Internet ports for accessing your system ..................................................................................................... 25
Network security considerations ................................................................................................................... 26
ABAP user roles and profiles .......................................................................................................................... 26
Certificates ....................................................................................................................................................... 26
5 Solution Provisioning in SAP Cloud Appliance Library .......................................................... 27
6 Appendix .......................................................................................................................................28
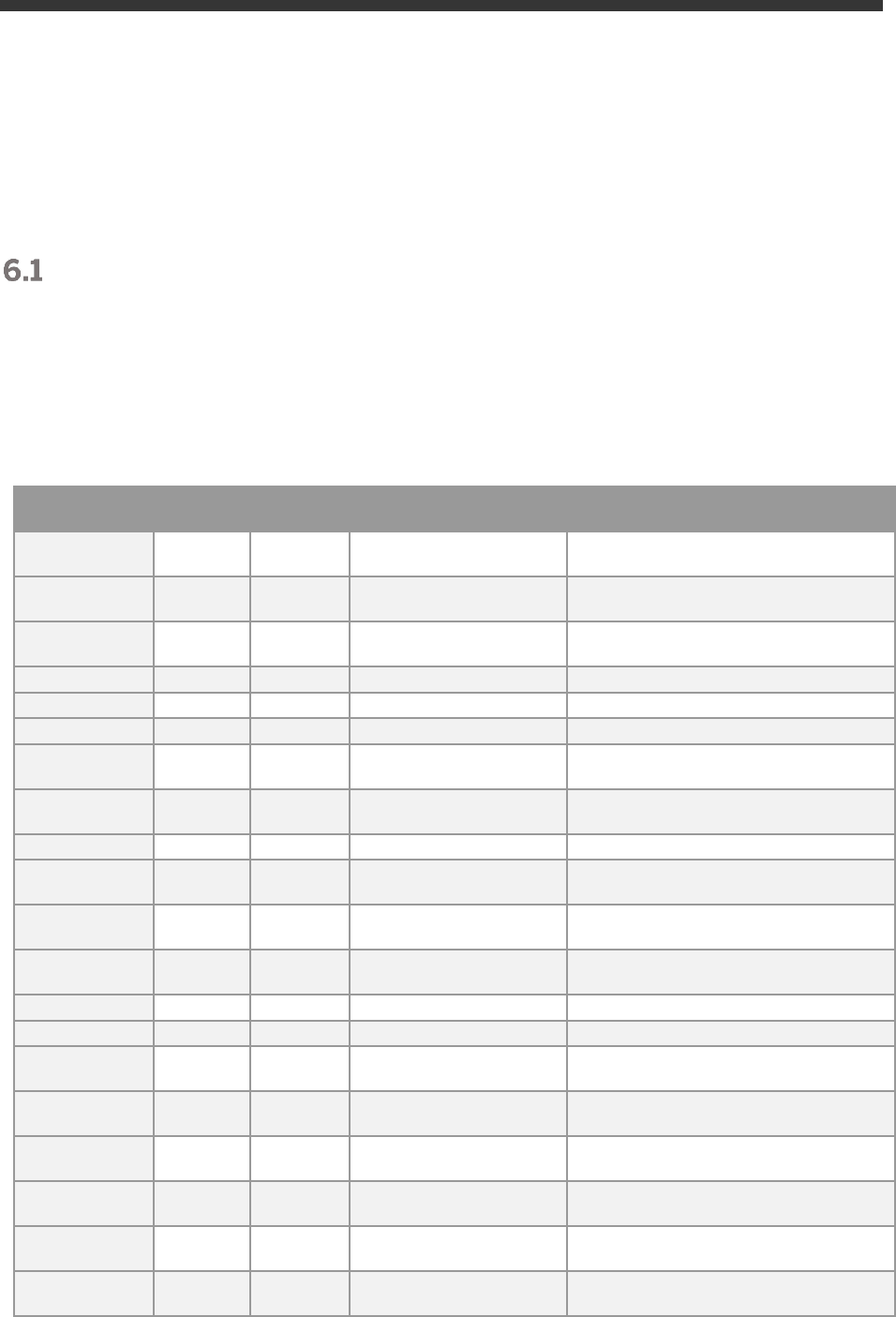
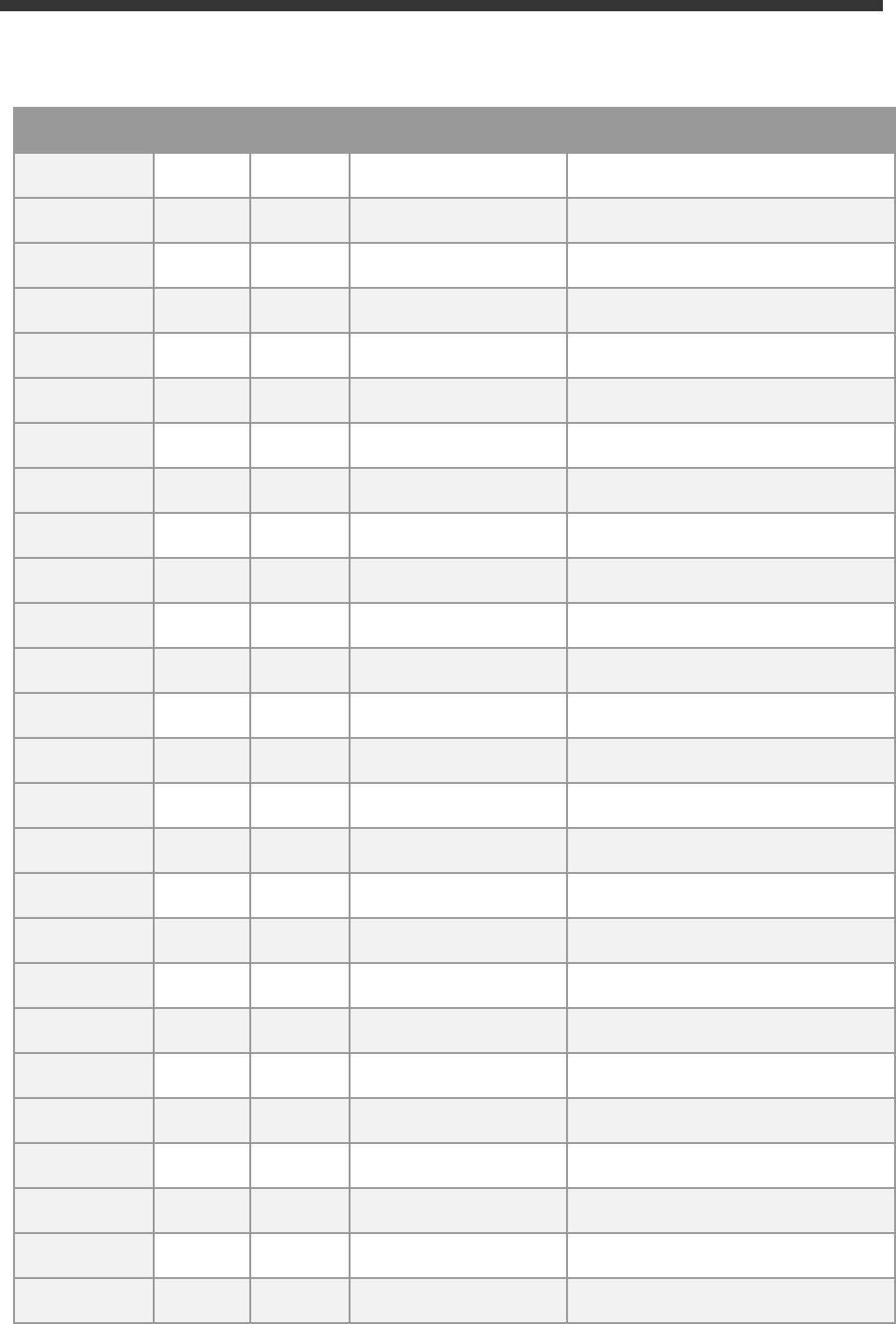
Installed Technical Component Details ......................................................................................................... 28
6.1.1 SAP ABAP application server 7.55 with SAP S/4HANA 2020 FPS01 & SAP HANA DB 2.0.54 .......... 28
6.1.2 SAP HANA Database Plug-In Versions ..................................................................................................... 34
6.1.3 SAP NetWeaver 7.50 application server JAVA with Adobe Document Services installed .................. 39
6.1.4 Windows Remote Desktop ......................................................................................................................... 40
6.1.5 SAP BusinessObjects BI Platform 4.2 ...................................................................................................... 40
4
1 Solution Information
Introduction
This guide provides information about the “SAP S/4HANA 2020 FPS01 Fully Activated Appliance” on SAP Cloud
Appliance Library (SAP CAL, https://cal.sap.com ).
The appliance contains an SAP S/4HANA 2020 (FPS01) system with pre-configured SAP Best Practices and
demo scenarios.
It can be rapidly brought up as your personal instance with administrative rights either hosted in dedicated cloud
providers such as Amazon, MS Azure or Google Cloud Platform (in ~2 hours) or on-premise on your own
hardware (in ~2-3 days).
Typical use cases are trial system, sandboxing, proof-of-concept, or scoping exercises.
The usage as a development system in implementation projects is not recommended since the appliance might
contain components and configuration settings (some with a separate license) that are conflicting with the later
deployment in a quality or production system.
A general introduction into the appliance and the usage as trial or sandbox system can be found on
https://blogs.sap.com/?p=727457
Known issues will be continuously updated in this blog: https://blogs.sap.com/?p=1215356
Post-installation steps and extensive demo guides with sample walkthrough scenarios can be found here:
https://blogs.sap.com/2019/04/23/sap-s4hana-fully-activated-appliance-demo-guides/.
Video tutorials how to create an AWS account and how to launch the appliance can be found here.
They might not necessarily show the creation of the SAP S/4HANA 2020 appliance (but another SAP solution
appliance), however, the concepts are the same.
5
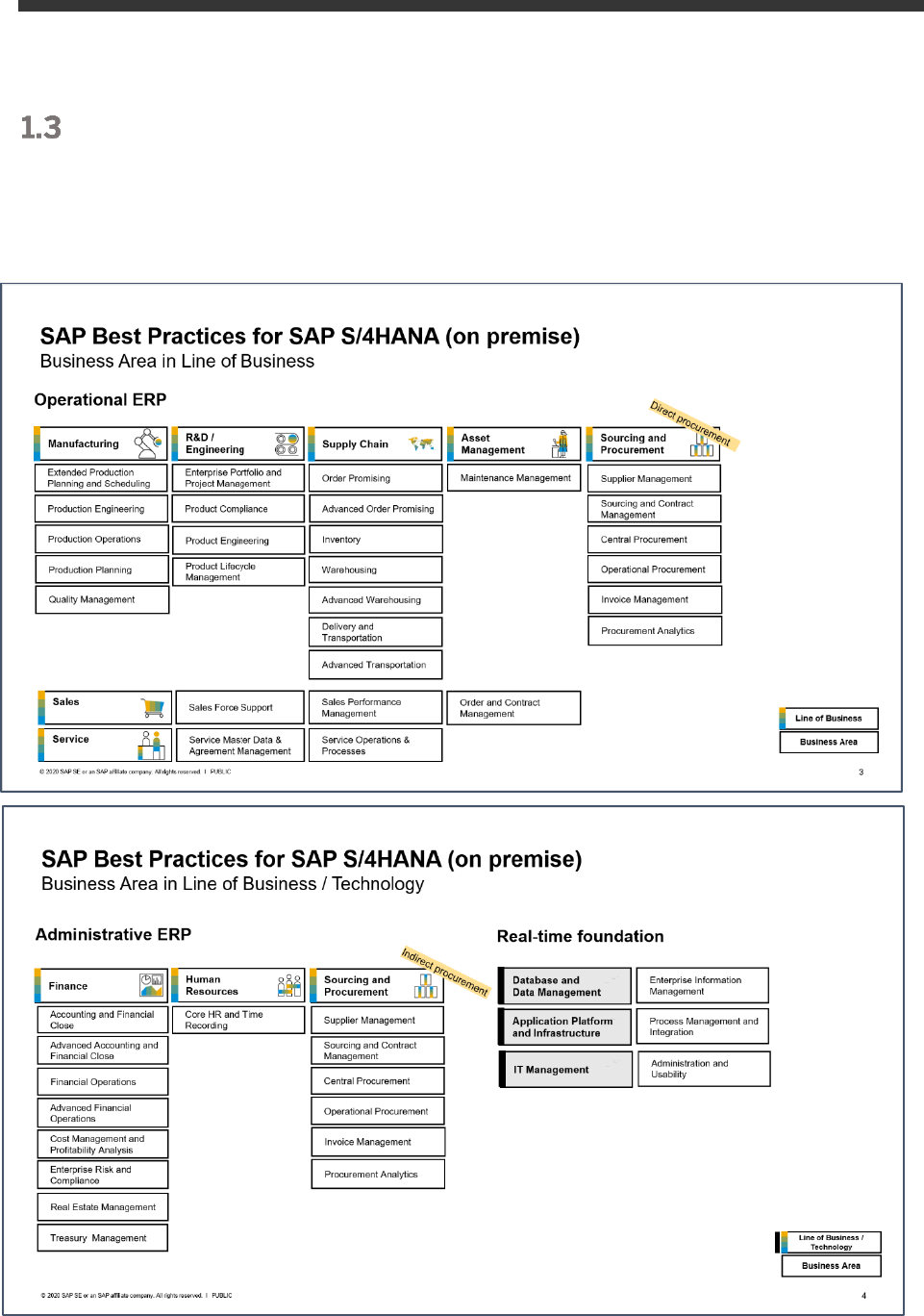
Installed Products
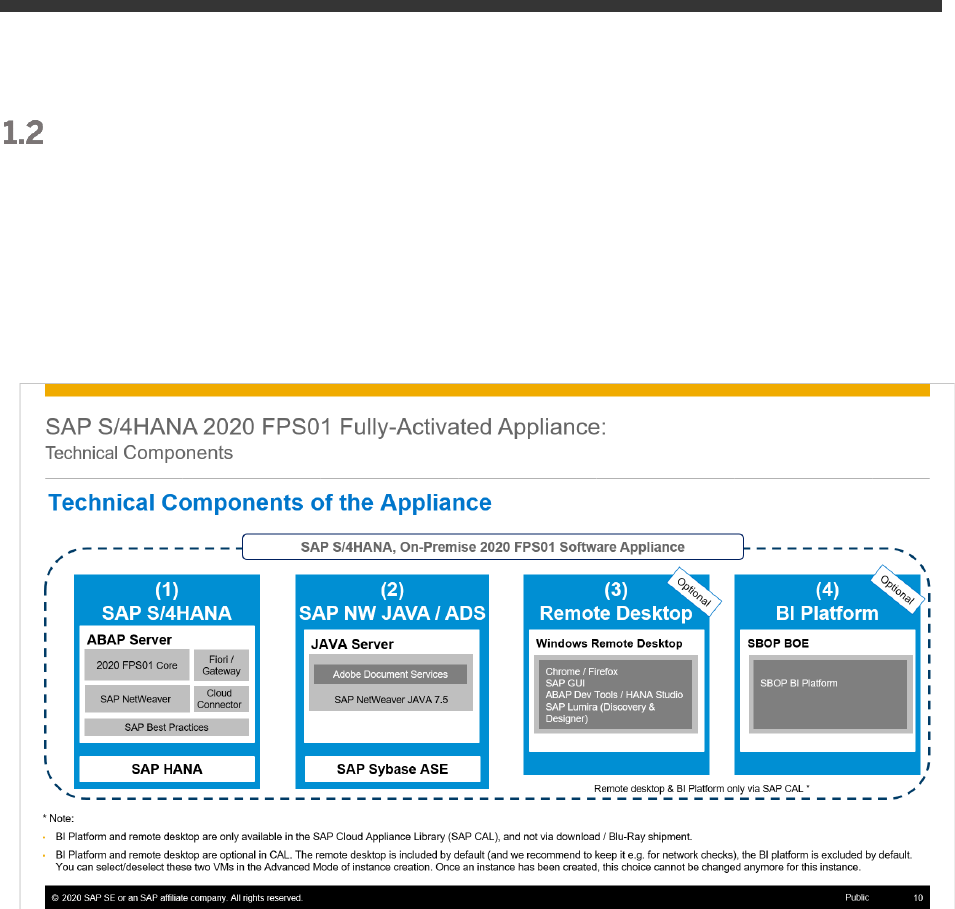
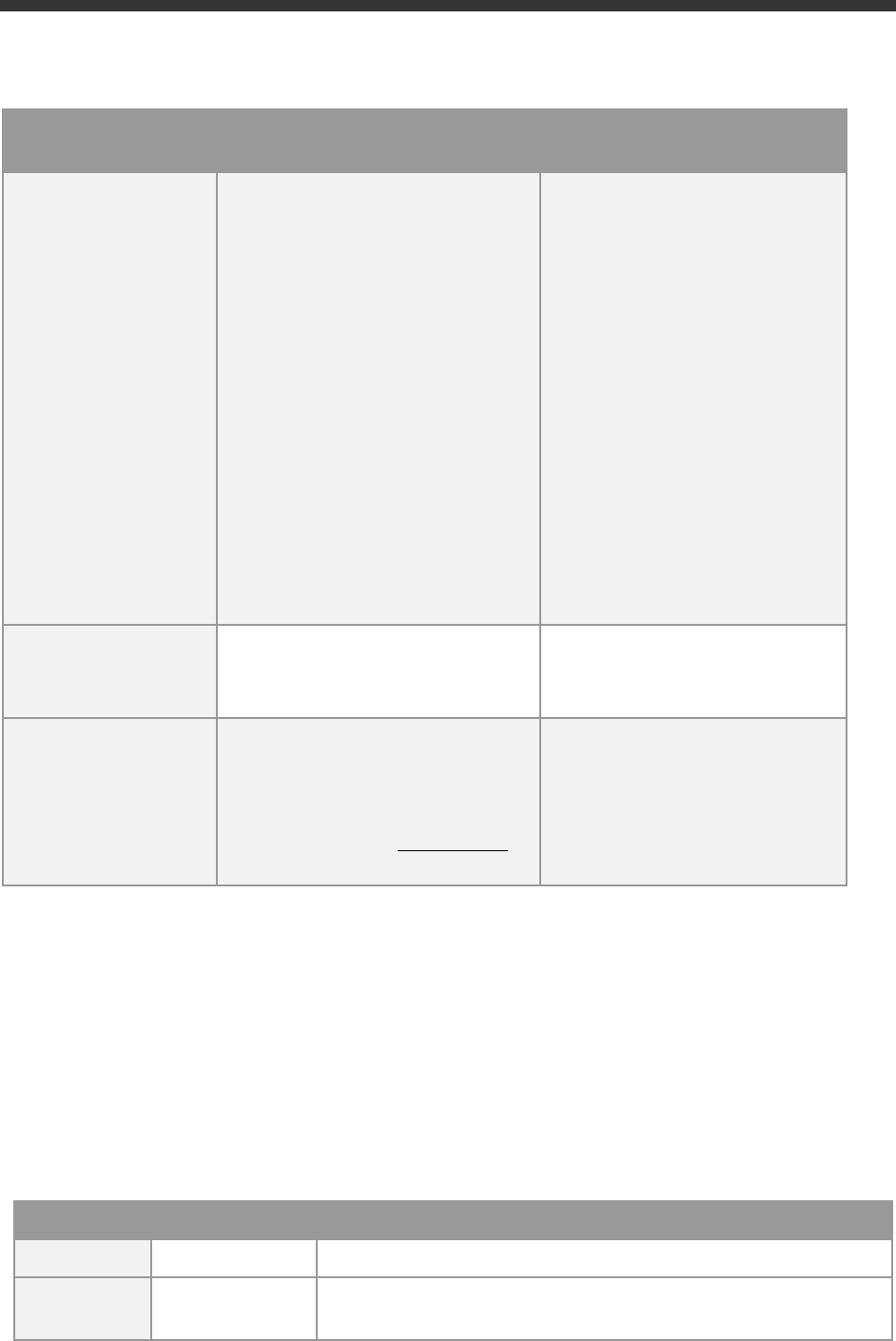
When you deploy the appliance (either in CAL or your own on-premise hardware), you get access to a system
landscape that has been built using the following components (see picture below).
1. SAP S/4HANA 2020 FPS01 (on SAP HANA database)
2. SAP NetWeaver 7.50 JAVA with Adobe Document Services (on Sybase ASE database)
3. Optional: Microsoft Windows Server 2016 (as remote desktop) for easy frontend access.
4. Optional: SAP BusinessObjects BI Platform 4.2 SP7
Notes:
• The virtual machines (VMs) for the BI Platform and the remote desktop (RDP) are optional in CAL You
can deselect these two VMs in the Advanced Mode of the instance creation. Once an instance has been
created, this choice cannot be changed anymore for this instance.
• The BI Platform and the remote desktop are only available when using SAP CAL as described in this
document. However, you can also receive the appliance for installation on your own on-premise hardware
but in that case BI platform and remote desktop are not included. Please see SAP Note 2041140 for the
option to install the appliance on your own hardware.
A detailed component list of the appliance can be found in the appendix of this guide.
7
In the appliance, the Best Practices have been fully activated, however, there are still areas that require additional
configuration to be fully functional.
The integration into other SAP products or 3
rd
party software is such an example where you need to specify at
least the credentials (tenant, account, etc.) of the integration target.
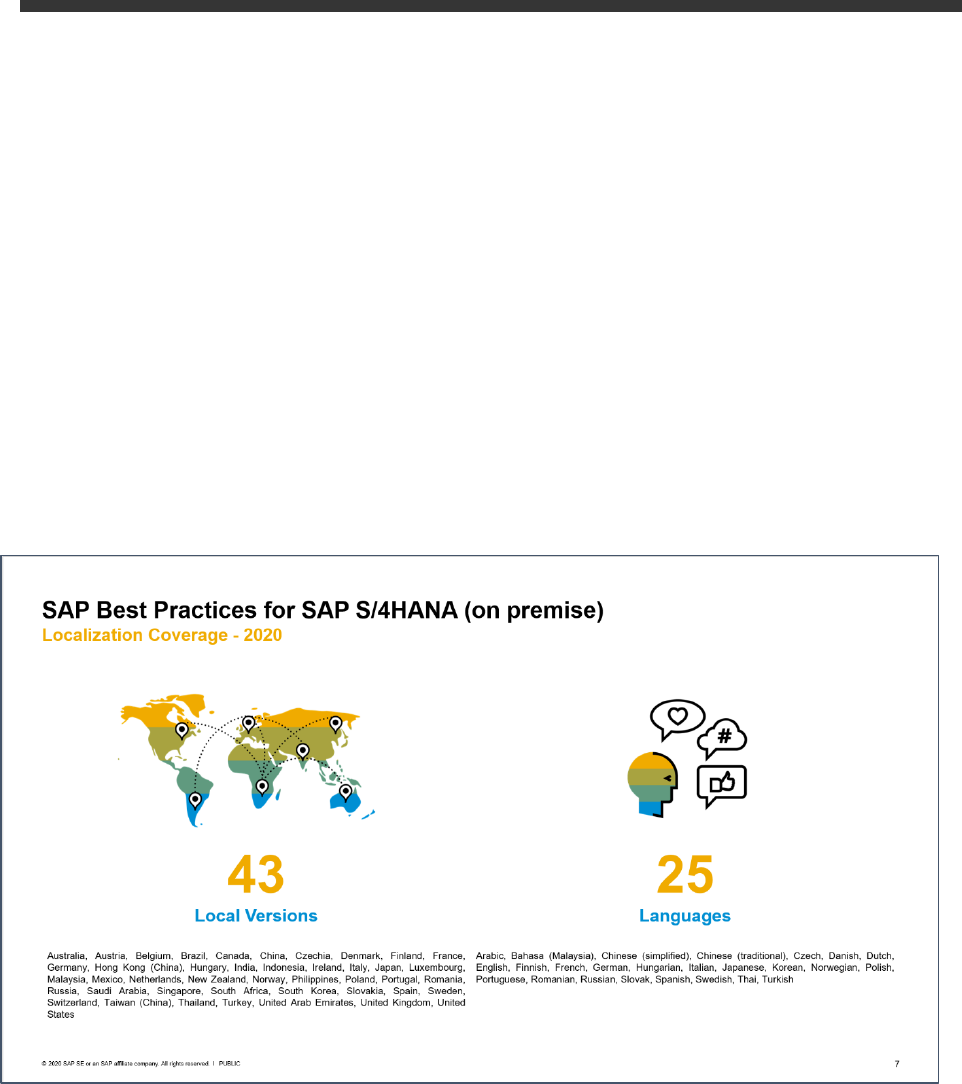
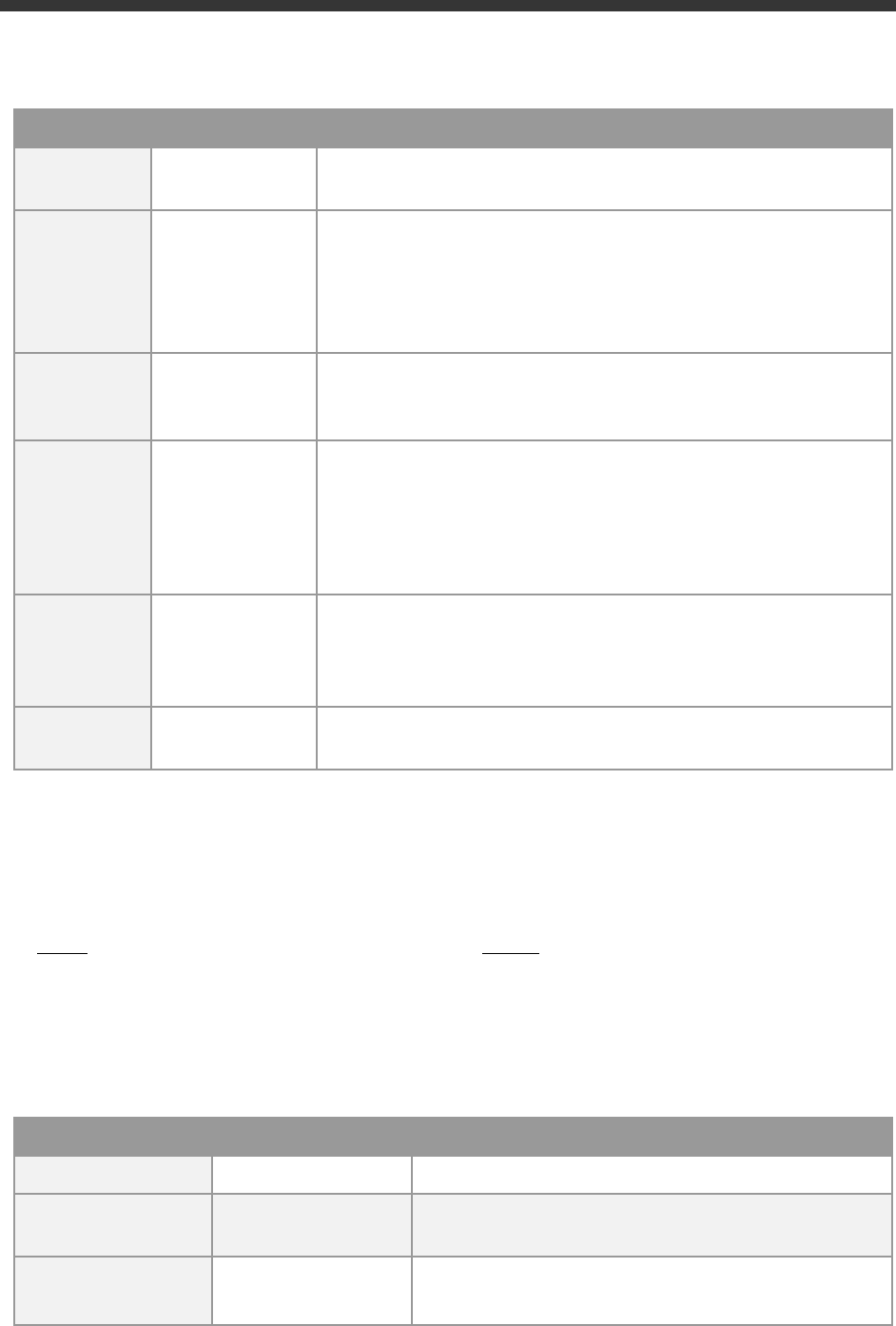
The SAP Best Practices configuration content of SAP S/4HANA 2020 is available for 43 local versions and 25
languages (see below slide).
In the appliance, all available localizations are activated in client 400 (see the section
ABAP client structure &
business users
later in this guide), however, the suggested demo walkthroughs incl. demo data in the appliance
are configured for USA only, using the company code 1710.
Besides the languages for SAP Best Practices, further language packages are installed in the system, but the
configuration content might not be fully translated into those.
8
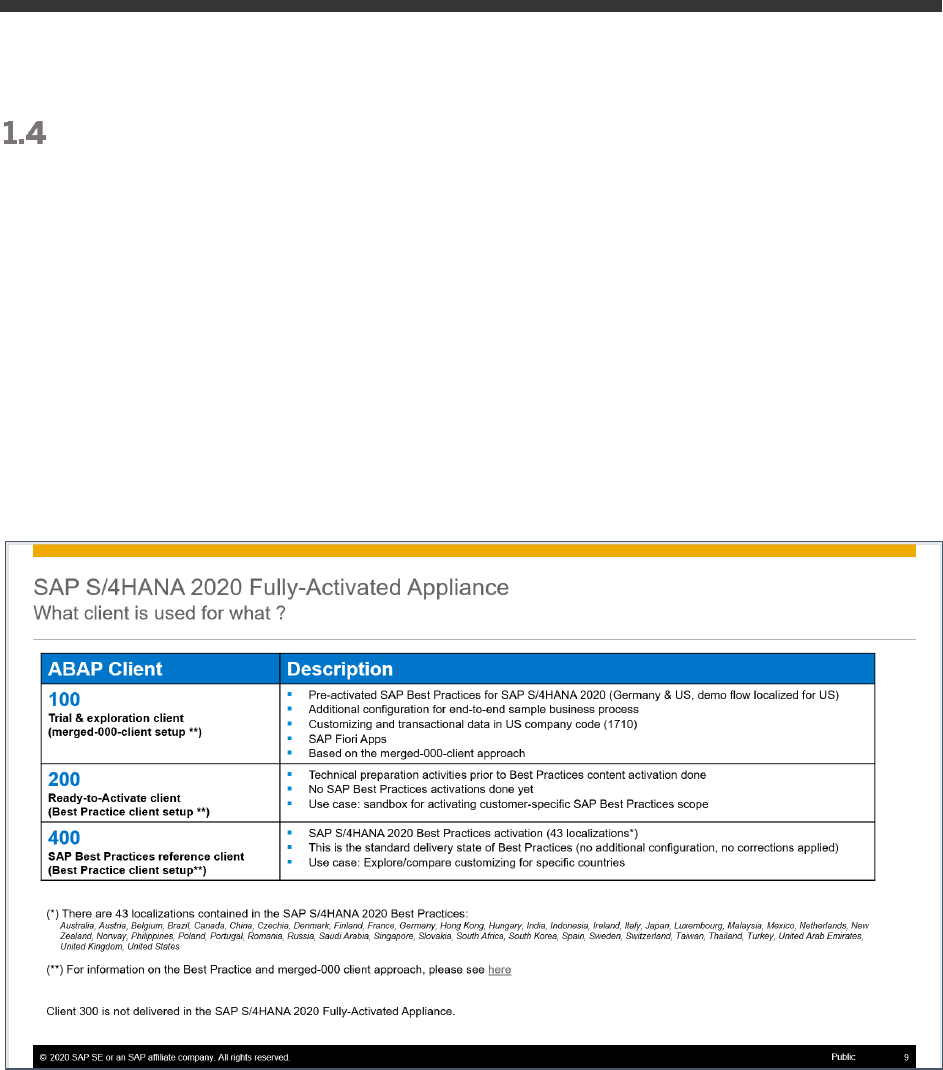
ABAP client structure & business users
Multiple ABAP clients are configured in the appliance:
• 000 serves as standard delivery client (as usual in on-premise deployments)
• 100 is the primary demo client that contains the pre-configured scenarios and sample data.
• 200 can be used for activating the SAP Best Practices on your own.
Please see the SAP Best Practices implementation guide for details. Be aware that some of the SAP
Notes and settings mentioned in the guide still need to be applied depending on what country or scope
you activate (e.g. the parameter rdisp/scheduler/prio_high/max_runtime is not set accordingly
yet as required by the guide).
• 400 contains the activated Best Practices based on the white-list approach
Please see chapter 2 for default users and logon procedures.
(*) For the US localization, SAP Best Practices are delivered with internal tax calculation. This includes sample
jurisdiction codes and sample rates so that you can execute the best practices test scripts. The organizational
structure and chart of accounts are activated with SAP Best Practices sample content. Client 200 does not
contain these settings.
(**) An explanation of Best Practice client and merged client can be found in the
Implementation Guide →
Prerequisite Settings → Setting up a new Best Practices Client - Client Setup Alternatives.
9
Sample Demo Walkthroughs
Once you have created a system instance in SAP CAL you will have a principally working S/4HANA system that
you can explore and change on your own.
To give you a jump-start into the contained scenarios, we have documented a wide range of example scenarios
that we recommend as starting point to get more familiar with the system.
Please see this blog (https://blogs.sap.com/2019/04/23/sap-s4hana-fully-activated-appliance-demo-guides/)
for the available demo guides (choose the applicable release).
Recommended Post-Installation Steps
As said above, your system instance will be a working system, however, there are certain settings that you might
need to adapt depending on your use case, for example:
1. Open the MM inventory management period for the current month if you intend to post goods
movements.
The above blog with the sample demo scenarios explains how to do this in section C) .
2. Check your customer/partner specific licenses and apply license keys.
Please see chapter 3 of this guide for details, in summary you will need to consider two timelines:
- If you intend to use the system beyond 30 days, you will need to possess licenses for SAP S/4HANA
and the SAP CAL
- If you intend to use the system beyond 90 days, you will need to generate and apply your own license
keys to the HANA DB, S/4HANA, and JAVA
3. Check further time-dependent settings if you face issues (this could be certain finance periods or tasks,
time-dependent production windows, and so on).
More Information & Support
1.7.1 More Information
Overview blog in SAP Community: https://blogs.sap.com/?p=727457
Known issues blog in SAP Community: https://blogs.sap.com/?p=1215356
Post installation steps and sample demo walkthroughs:
(https://blogs.sap.com/2019/04/23/sap-s4hana-fully-activated-appliance-demo-guides/

10
SAP S/4HANA Trial Landing Page (also containing a “Quick Start Guide” how to set up the appliance)
https://www.sap.com/cmp/oth/crm-s4hana/s4hana-on-premise.html
YouTube playlist (how to create Cloud Provider accounts, start an SAP S/4HANA appliance instance, etc):
https://www.youtube.com/playlist?list=PLWV533hWWvDmww3OX9YPhjjS1l1n6o-H2
1.7.2 Support
If you run a 30-day trial (i.e. no SAP CAL subscription license), please use the SAP Community (preferably take
SAP CAL as it’s closely monitored):
• SAP CAL (for CAL usage, access, etc.): https://answers.sap.com/questions/metadata/24005/sap-
cloud-appliance-library.html
• SAP S/4HANA (for S/4 specific functional questions):
https://answers.sap.com/questions/metadata/22943/sap-s4hana.html
If you have an SAP CAL subscription license acquired, you can also report an incident (component BC-VCM-CAL).
11
2 Accessing the Solution
Overview
The appliance can be accessed via a preconfigured Windows remote desktop (option 1) or via client tools on your
local PC (option 2).
For first steps with the appliance, we recommend access via the remote desktop since you only need to have the
Windows remote desktop client installed on your PC which in most cases will be the case,
Since UI performance are usually better via access from your local PC, please evaluate if you can use this method
as standard access. It requires administrator access on your PC and 5 minutes of effort.
Option 1: System access via embedded Windows Remote
Desktop frontend server
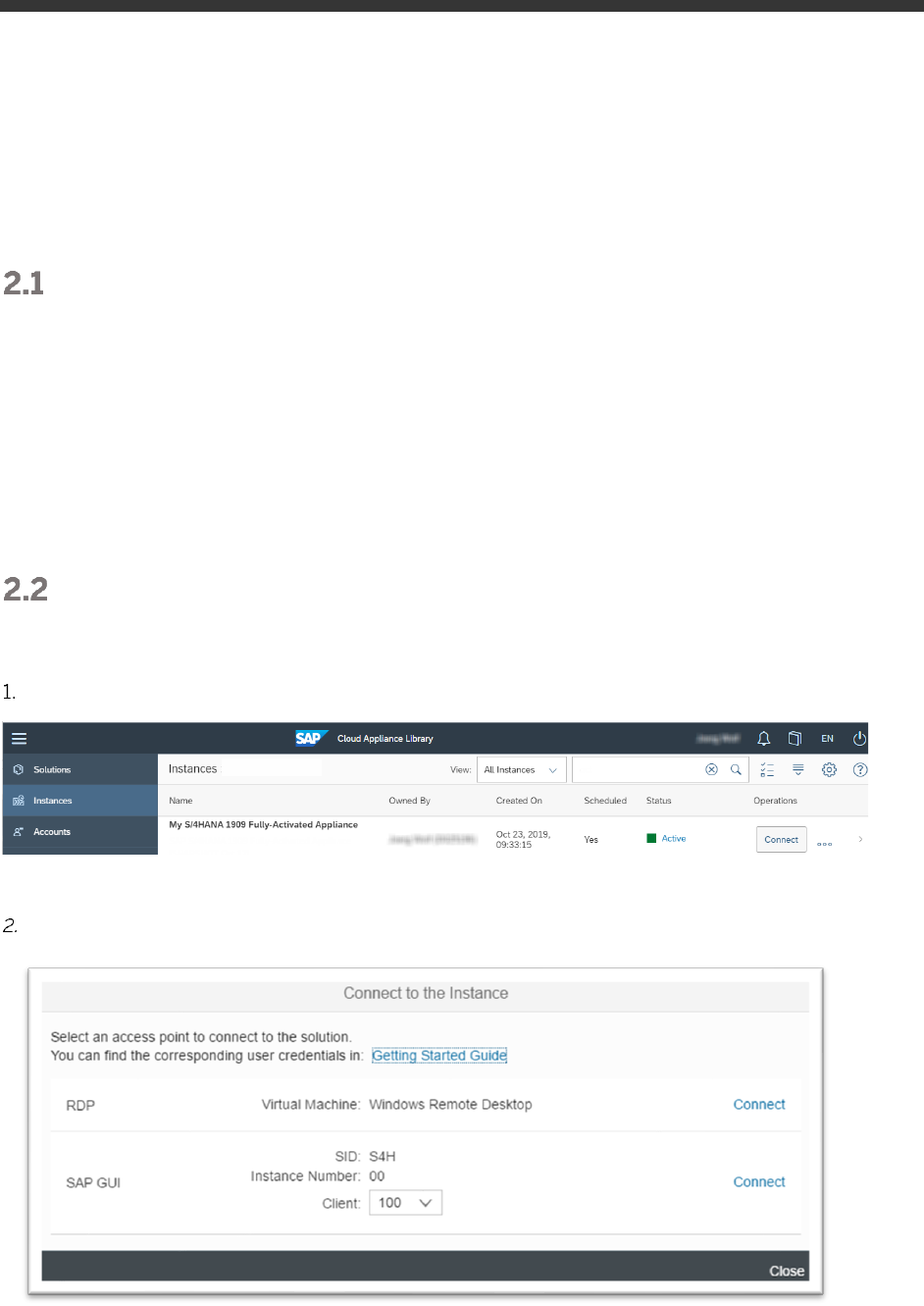
After your own solution instance is created, click the Connect button in the Instances view of the console.
In the pop-up, click Connect in the “RDP Virtual Machine: Windows Remote Desktop” line.
12
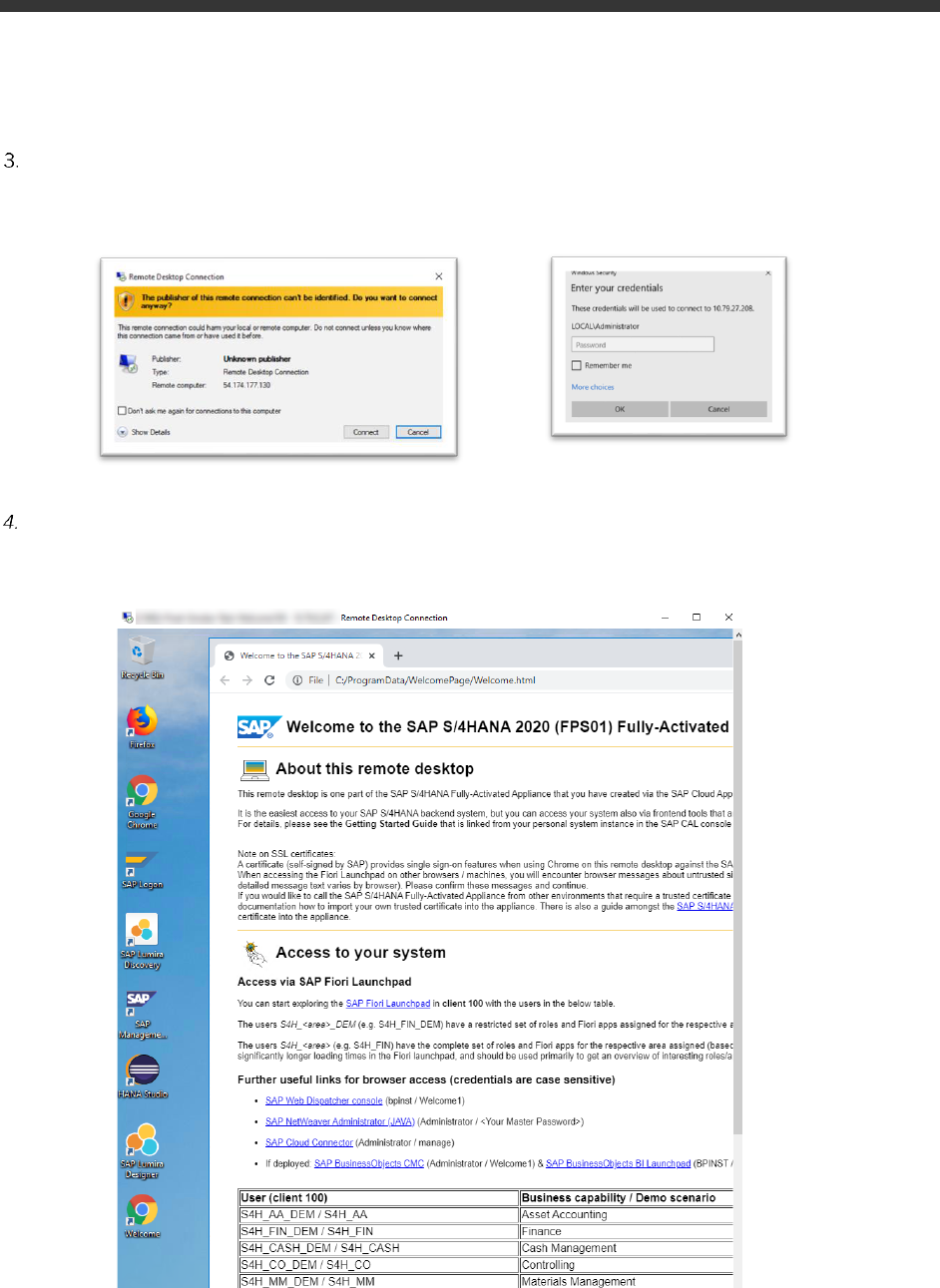
Confirm the pop-up window to allow Remote Desktop Connection (click on “Connect”).
Enter user Administrator (local domain of the remote desktop) and your <Master Password> that you
specified during the instance creation in the SAP CAL console.
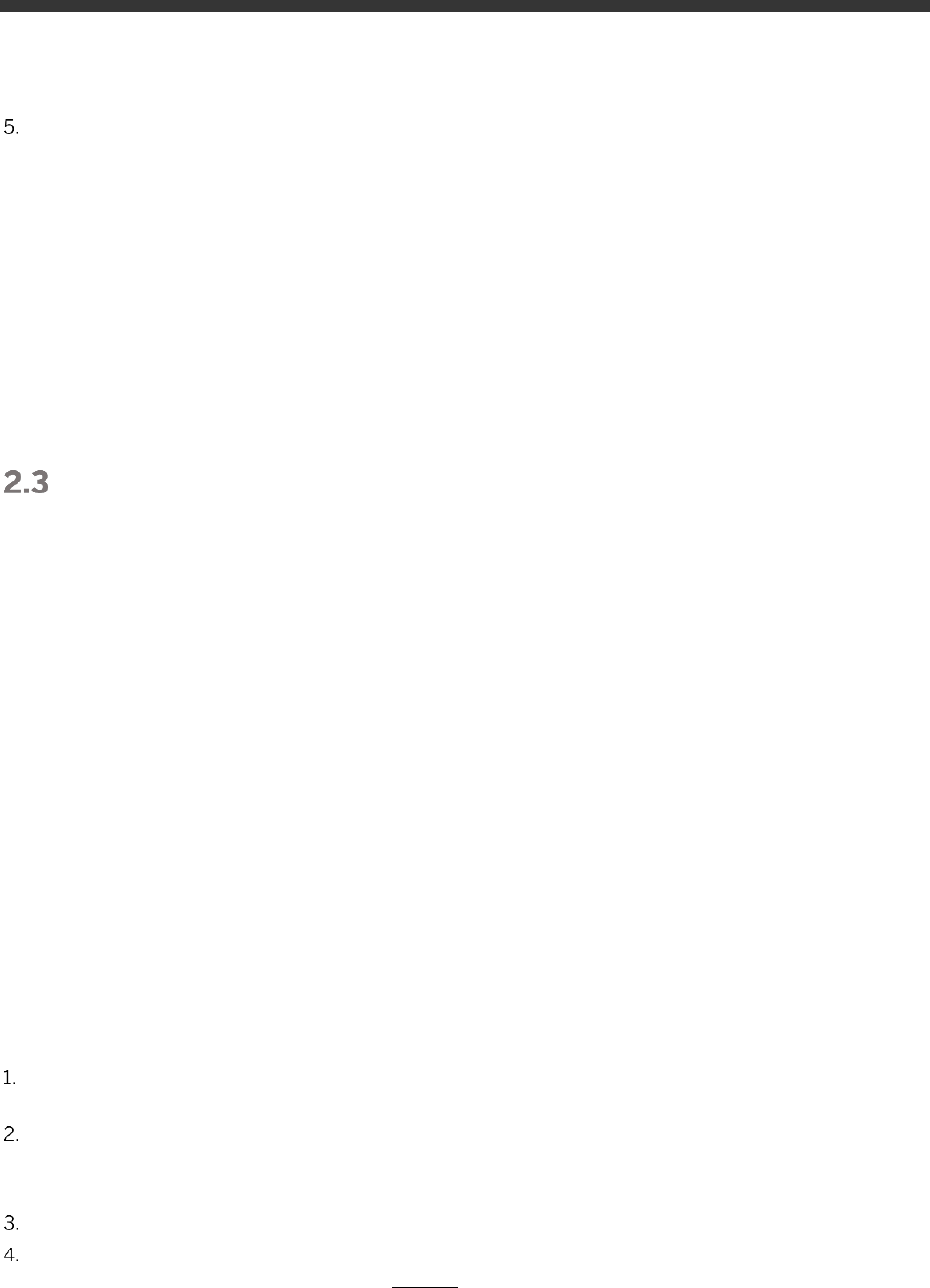
Next you will see the pre-configured Windows Frontend Server. Follow the information on the Welcome page
(start link also on desktop if it doesn’t come up automatically) to logon to the SAP S/4HANA system, and to
run sample scenarios. More details on system connectivity can be found in section 3.3.
13
Further remarks:
- The embedded Windows Remoted Desktop license allows 2 concurrent sessions (e.g. one for the
existing user Administrator and one for another user that you can create on the remote desktop).
Installing your own RDP license might also be an option to allow more concurrent users on the RDP.
- If your cloud provider infrastructure has restricted Internet access (e.g. it is a fenced environment),
the remote desktop might not be fully provisioned
o Chrome is not installed → use Firefox for Fiori access or install Chrome at a later point in
time if this is possible in your network setup
o The Welcome page will not show up on the desktop, but you can find it on the remote
desktop in the folder Q:\flavor\S4HANA_Fully_Activated\WelcomePage.
Option 2: System access via local PC
2.3.1 Mapping your local
/etc/hosts
file
To log on to the Fiori Launchpad from your local PC, you need to ensure that you have mapped the IP addresses of
your instance against clear text host names. This mapping step is needed since the connection to the cloud
providers uses IP addresses, whereas the S/4HANA system needs dedicated host names to work correctly.
After you have done the mapping (by editing a local file on your computer), you will be able to access the Fiori
Launchpad of SAP S/4HANA via this URL:
https://vhcals4hcs.dummy.nodomain:44301/sap/bc/ui5_ui5/ui2/ushell/shells/abap/FioriLaunchpad.html
If you cannot map your local hosts file (e.g. you don’t have administrator rights on your computer), you can use
the IP address of your instance in the URL (https://<IP_Address>:44301/...), however, not all applications and
scenarios will work correctly with it e.g. WebGUI or Web Dynpro applications will not display in the browser.
Another option could be to use browser plugins (e.g. Chrome Virtual Host) that simulate the mapping in the
browser session only. Again, not all scenarios might work correctly with it.
The following describes how to modify the local hosts file on a Windows computer.
Open Notepad as administrator (search for Notepad on your computer > Right mouse click > Run as
administrator):
Click File → Open and enter the following path:
For Windows operating system: c:\windows\system32\drivers\etc\hosts
For Linux operating system: /etc/hosts
Ensure to select All Files (*.*)
Open the hosts file and add the following lines to it (the IP addresses for the servers are displayed in the CAL
console in the instance properties, take the external IP address):
# S4H Appliance
<External IP Address SAP S4HANA/HDB server> vhcals4hci.dummy.nodomain vhcals4hci
vhcals4hcs.dummy.nodomain vhcals4hcs vhcalhdbdb vhcaldhbdb.dummy.nodomain
14
<IP Address SAP NW JAVA/ASE/ADS server> vhcalj2eci.dummy.nodomain vhcalj2eci
vhcalj2ecs.dummy.nodomain vhcalj2ecs vhcalj2edb vhcalj2edb.dummy.nodomain
<IP Address SAP BI Platform > bihost bihost.dummy.nodomain
Save the hosts file and exit.
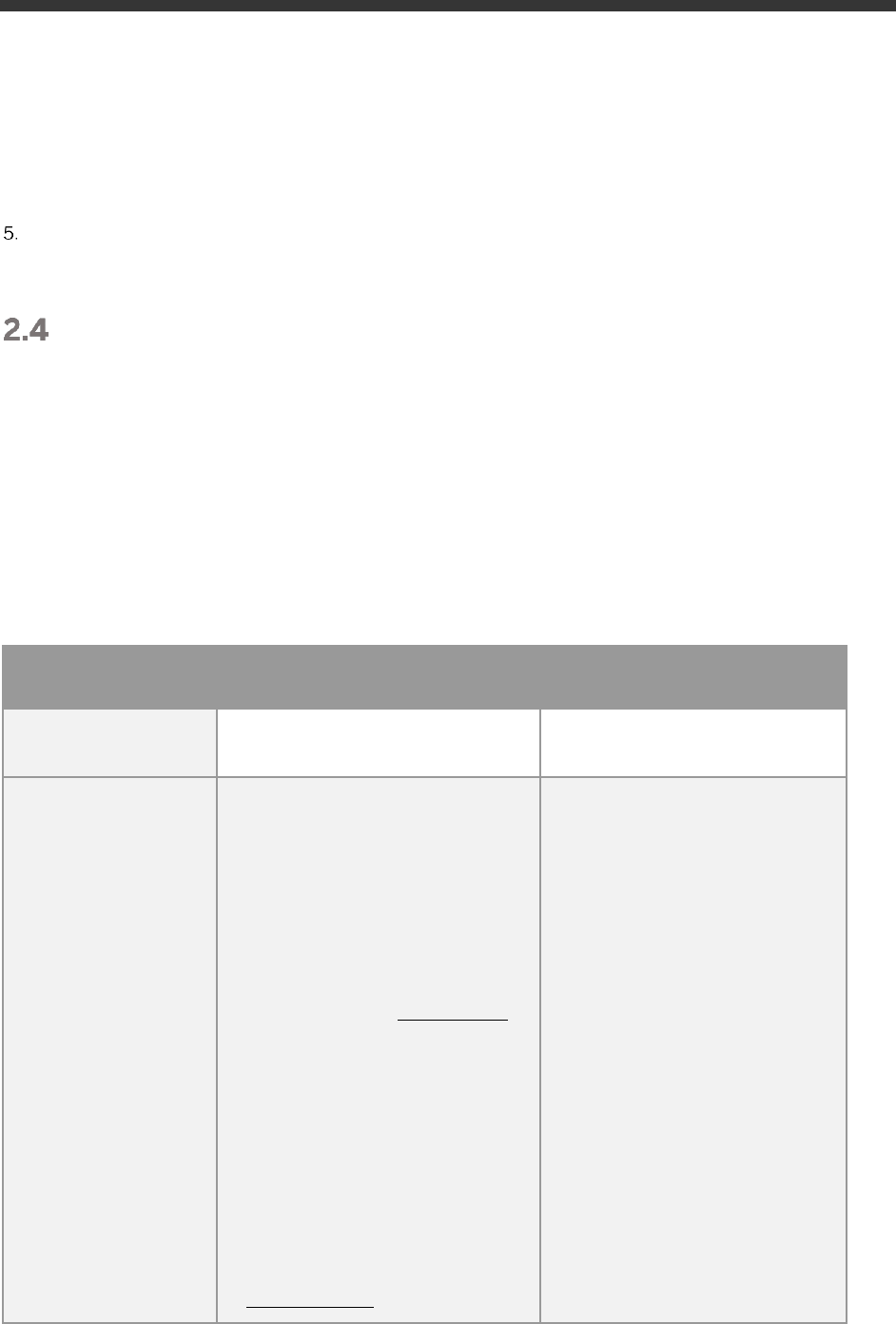
Users & passwords for the system components
Note upfront: For URLs starting with vhcal… you will need to map your /etc/hosts file as described in chapter 2.3.
2.4.1 SAP S/4HANA ABAP application server
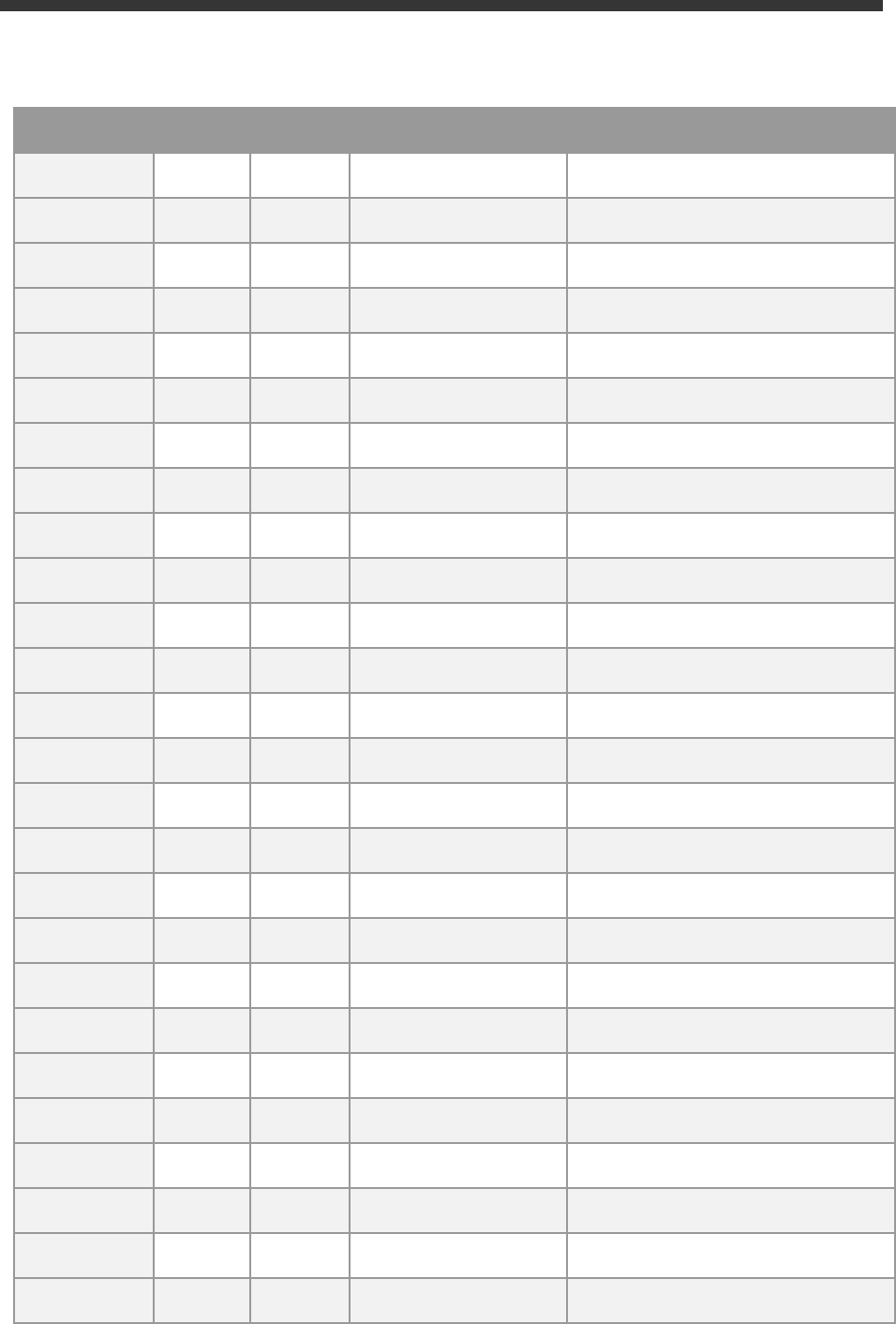
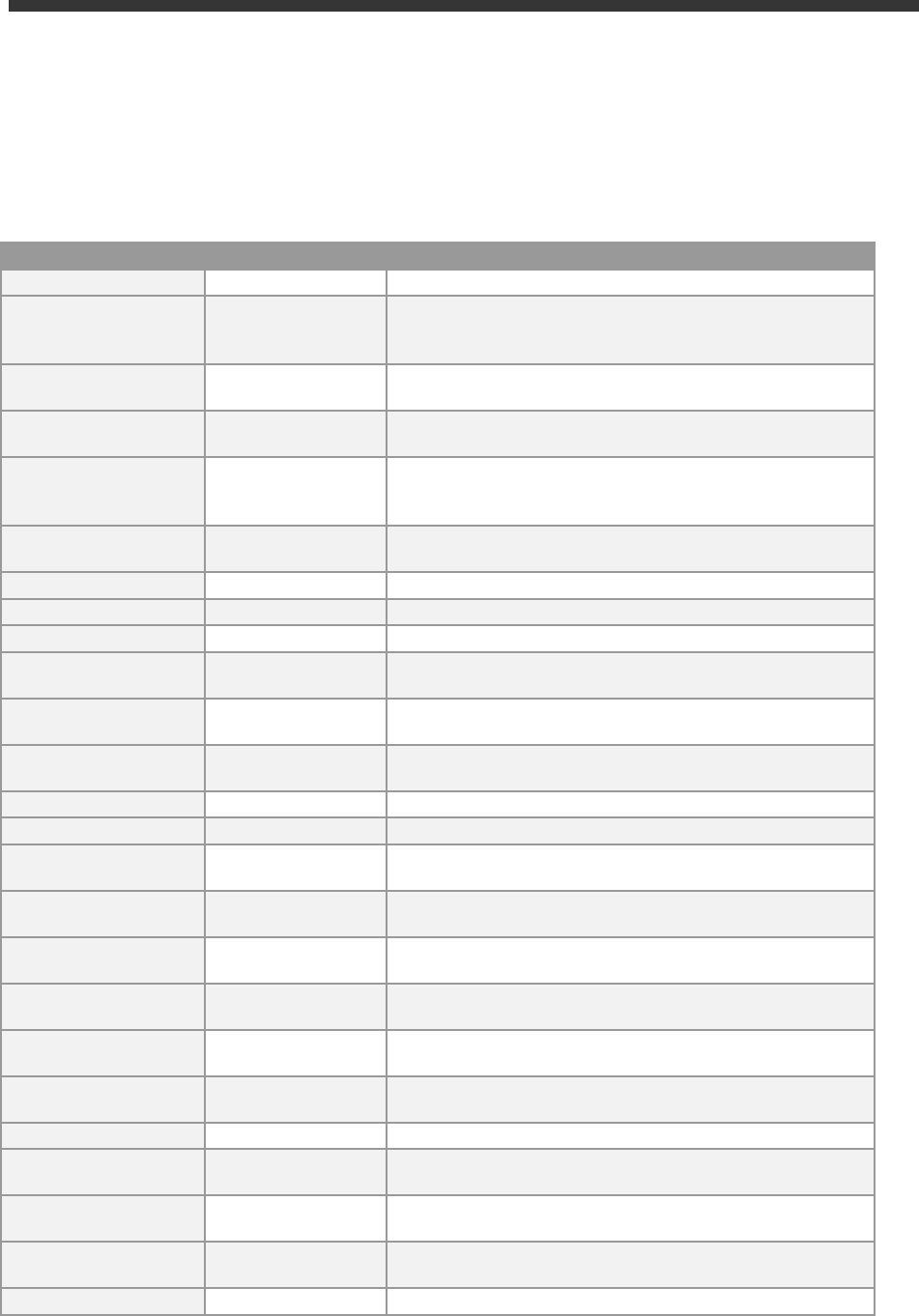
2.4.1.1 Pre-configured business users in SAP S/4HANA
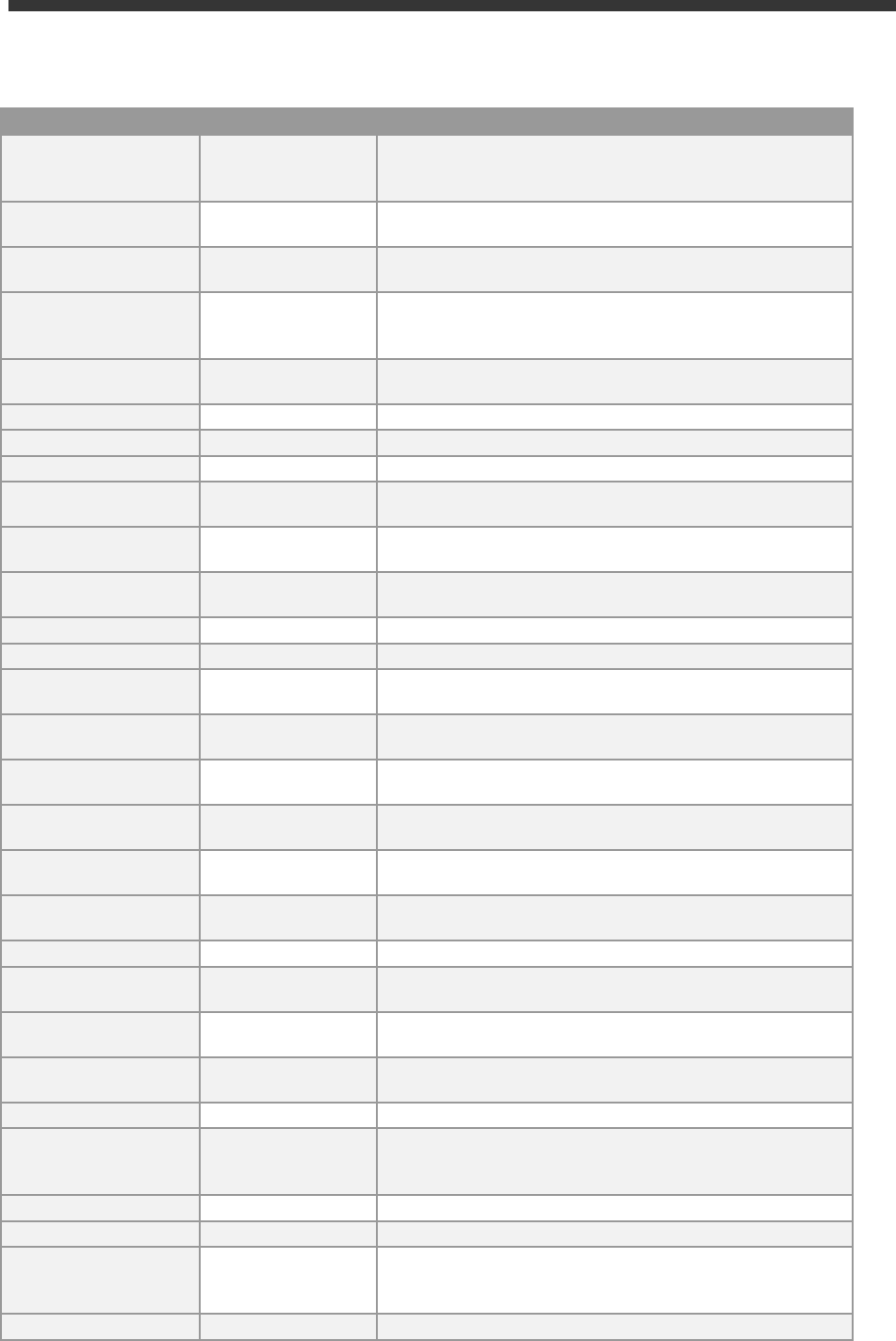
Client
Business Content
Sample users
(password
Welcome1 if not noted otherwise
)
000
Standard delivery client
• Nothing specific
(standard customizing only)
• BPINST
• DDIC / SAP* (<Master_Password>
100
Trial & Exploration client
• Pre-activated SAP Best
Practices for SAP S/4HANA
2020 (Germany & US, sample
demo flow localized for US) *
• Customizing and
transactional data in US
company code (1710)
• SAP Fiori Apps
• Based on the merged-client
approach
• BW configuration for
Integrated Business Planning
(IBP)
Note on the users:
•
S4H_AA_DEM / S4H_AA
(Asset Accounting)
•
S4H_FIN_DEM / S4H_FIN
(Finance)
•
S4H_CASH_DEM / S4H_CASH
(Cash Management)
•
S4H_CO_DEM / S4H_CO
(Controlling)
•
S4H_MM_DEM / S4H_MM
(Materials Management)
•
S4H_PP_DEM / S4H_PP
(Production Planning
•
S4H_SD_DEM / S4H_SD
(Sales & Distribution)
•
S4H_EXT
(Extensibility)
•
S4H_EWM_DEM
(Warehouse Management)
•
S4H_DDR_DEM
(Demand-Driven Replenishment)
•
S4H_PPM_...
(Portfolio & Project Management)
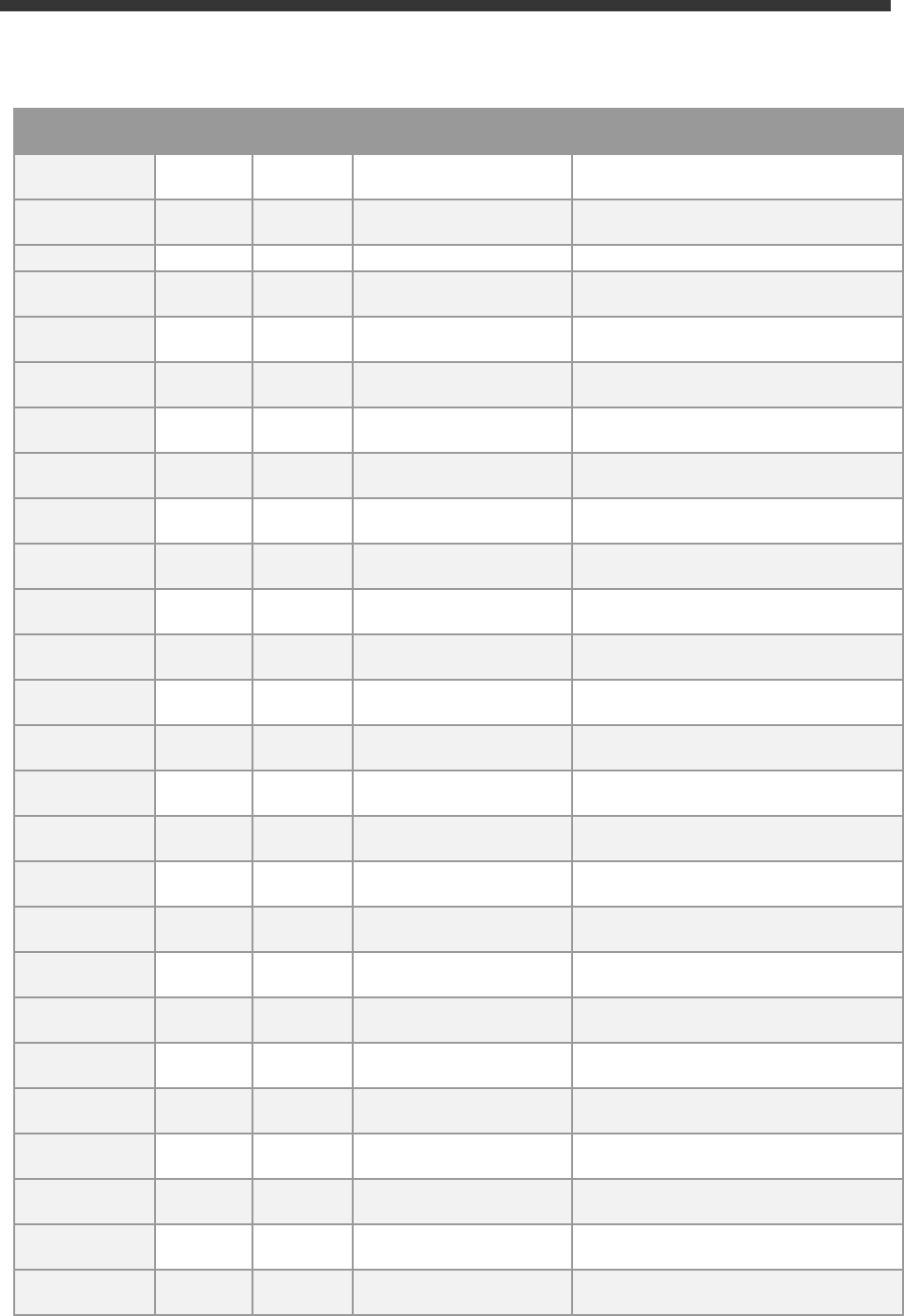
15
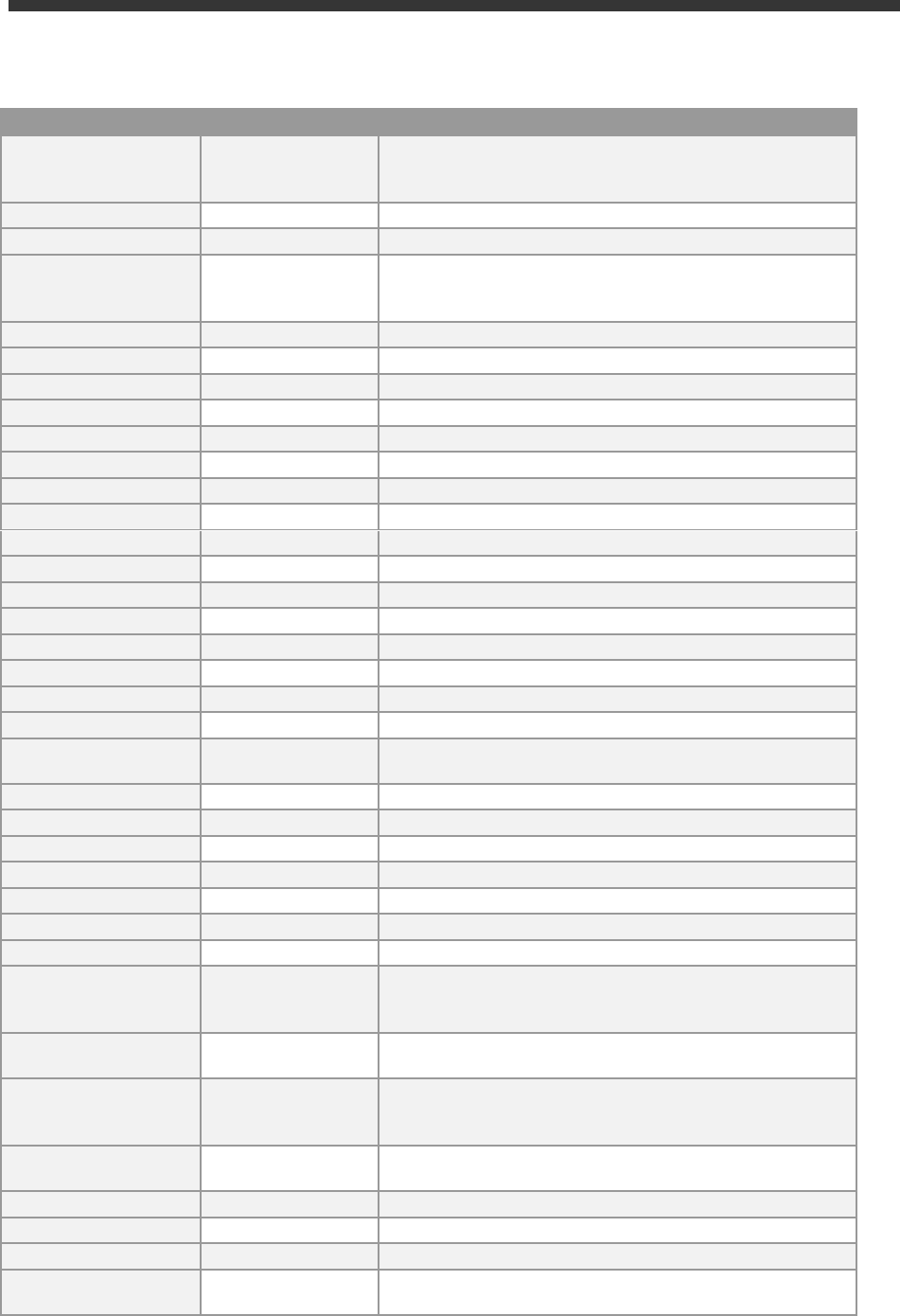
Client
Business Content
Sample users
(password
Welcome1 if not noted otherwise
)
The users S4H_<area>_DEM (e.g.
S4H_FIN_DEM) have a restricted set of
roles and Fiori apps assigned for the
respective area, and should be primarily
used for the suggested demo
walkthroughs.
The users S4H_<area> (e.g. S4H_FIN)
have the complete set of roles and Fiori
apps for the respective area assigned
(based on our assessment in the context
of the appliance). These users will have
significantly longer loading times in the
Fiori launchpad, and should be used
primarily to get an overview of interesting
roles/apps, and to serve as template for
your own user creation in transaction
SU01.
•
S4H_TM_DEM
(Transportation
Management)
•
S4H_PAI
(Predictive Analytics)
•
S4H_MG
(Data Migration)
•
SERV_EMPL / SERV_MAN /
SLS_MAN / IC_AGENT_SRV
(SAP S/4HANA Service)
•
MDG_...
(Master Data Governance)
•
S4H_HCM_…
(Human Capital Management)
•
FIORIADMIN (
Fiori customizing &
roles)
•
BPINST
(Generic user. Caution: very long
loading times in Fiori Launchpad)
200
Ready-to-Activate client
(white list)
• Ready-to-Activate client with
all pre-activation preparation
activities executed
BPINST / DDIC / SAP*
400
SAP Best Practices
reference client
(white-list)
• Pre-activated SAP Best
Practices for SAP S/4HANA
2020 without transactional
data
• Based on the merged-client
approach
BPINST / DDIC / SAP*
All above users have the default password
Welcome1
if not indicated otherwise.
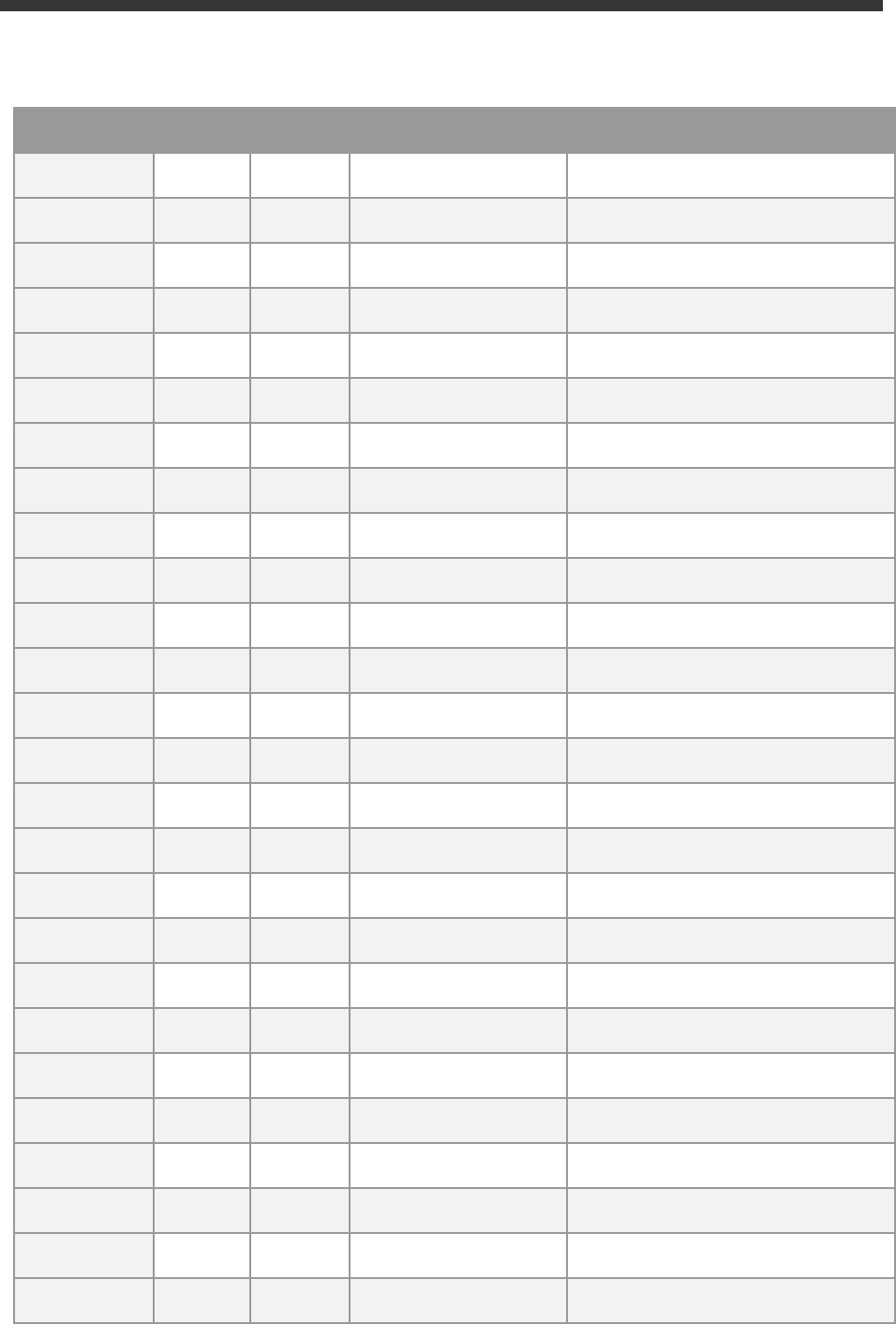
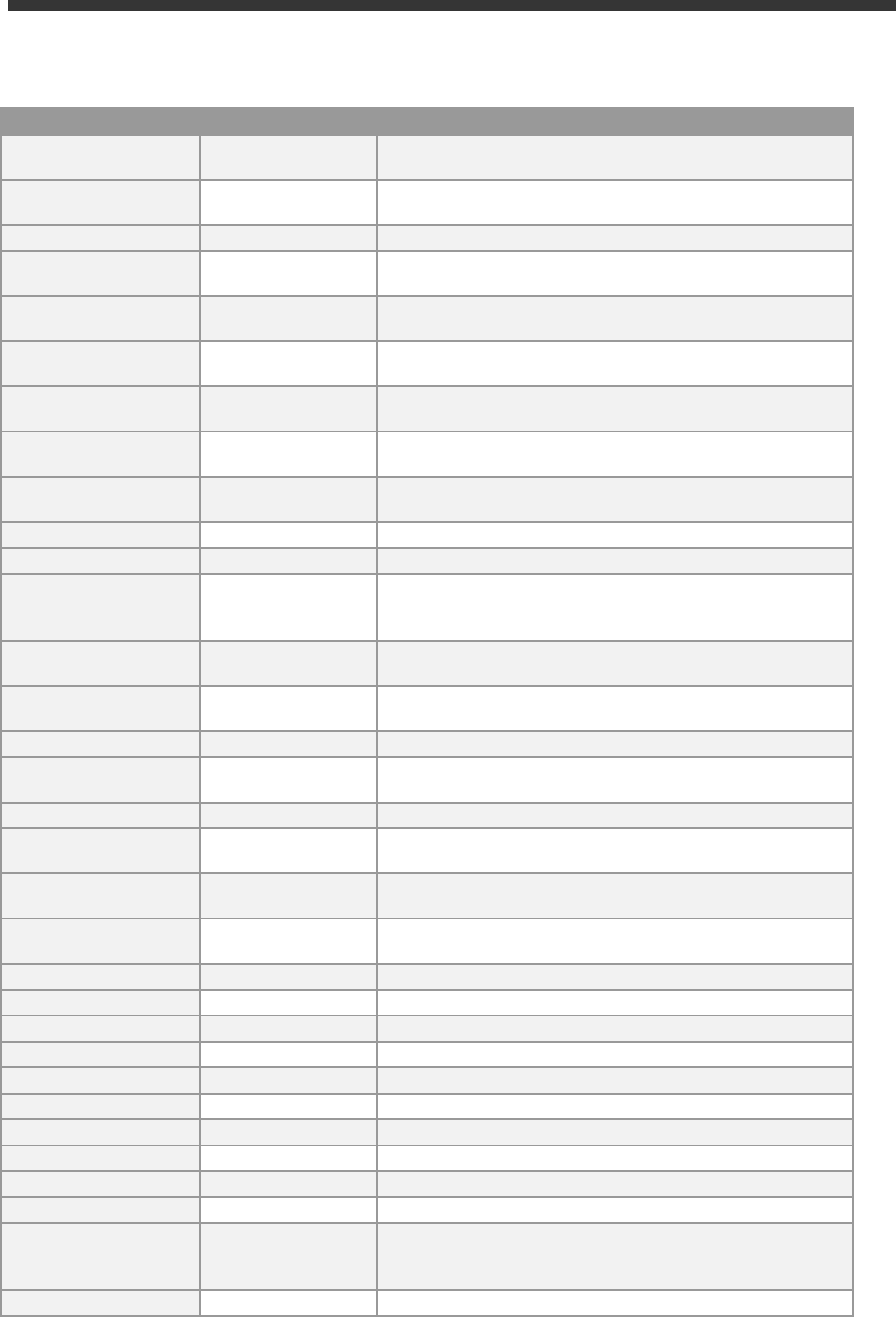
2.4.1.2 Administrative data & users for SAP S/4HANA
Connect to SAP S4H using the information in the table below (URLs with the host name vhcal… require hosts file
mapping before, see chapter 2.3).
Name
Value
Description
SID
S4H
System ID of the SAP system
Instance
Number
00
The instance number of the central instance (CI)
16
Name
Value
Description
Clients
See section 1.4
These are the pre-configured clients, see section “Business Scenarios
& Localizations” for details
Password for
users DDIC &
SAP*
<Master
Password>
in
client 000.
Welcome1
in other
clients
The master password is the password that you chose in the SAP Cloud
Appliance Library when creating the instance.
ABAP
administrator
s4hadm /
<Master
Password>
Additional user for ABAP lifecycle management – start/stop,
administration,
SAP Web
Dispatcher
administrator
webadm /
VA1MPwd_
or
bpinst /
Welcome1
Access to Web Dispatcher console:
https://vhcals4hcs.dummy.nodomain:44301/sap/admin/public/defa
ult.html
bpinst is case sensitive.
Technical user
for HANA DB
connectivity
(schema user)
SAPHANADB /
<Master
Password>
See tCode
DBACOCKPIT → System Landscape → Database
Connections
for additional usage of the SAPHANADB user
SAP Cloud
Connector
Administrator /
manage
Initial credentials for the integrated SAP Cloud Connector (access via
https://vhcals4hcs,dummy.nodomain:8443)
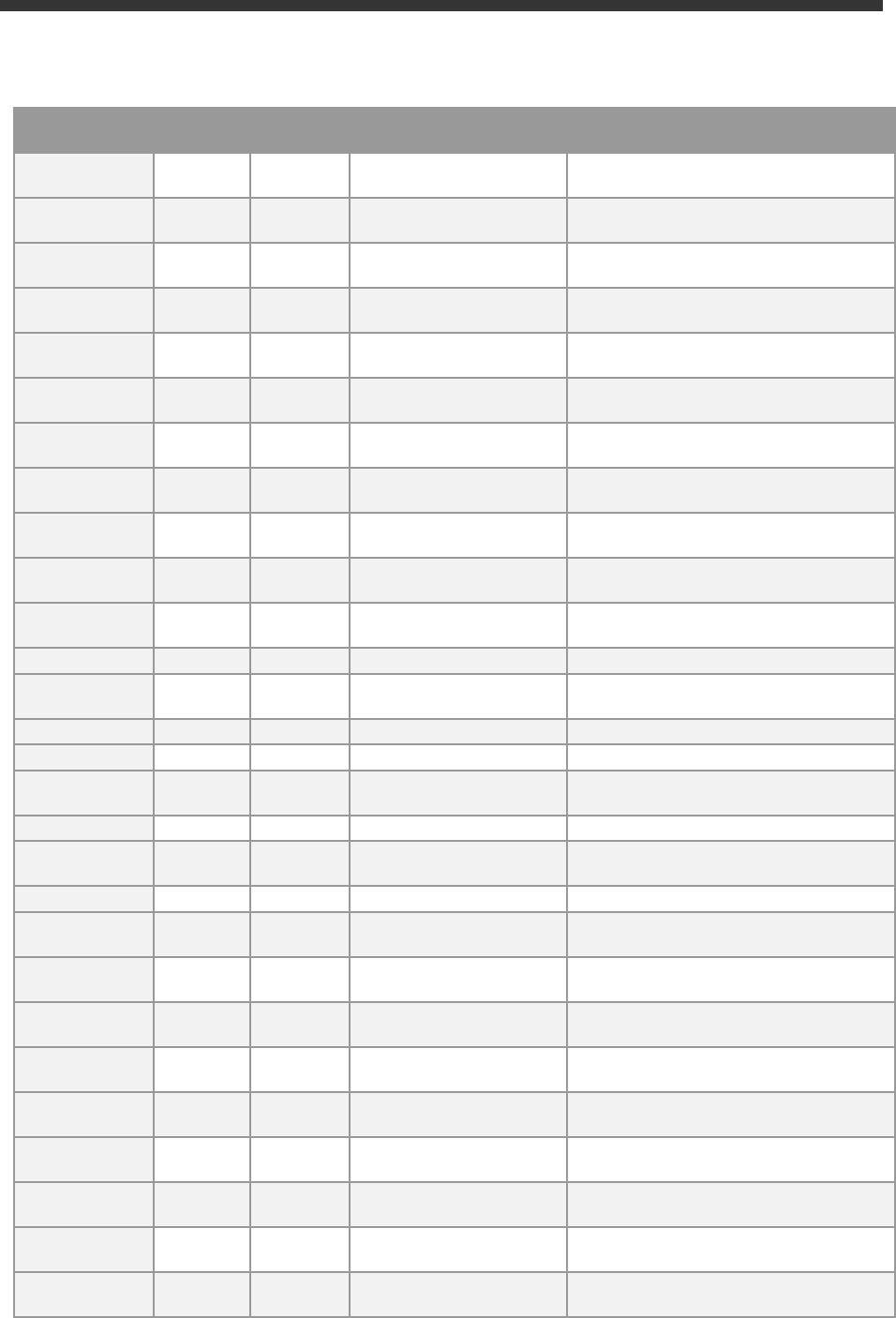
2.4.2 SAP HANA DB server
Two database entities are relevant for the appliance:
The tenant database (for storing the S/4HANA data) and the system database (for general data and settings e.g.
maintaining the license key for SAP HANA).
An entry for both is pre-configured in the HANA Studio on the remote desktop but you can also add entries in your
local HANA Studio.
Tenant database (use Single Container when adding it to your local HANA Studio)
Name
Value
Description
HANA DB system
HDB
System ID of the HANA DB
HANA DB Instance
Number
02
Instance number of HANA DB
HANA SYSTEM user
name
SYSTEM /
<Master Password>
Standard HANA system user
17
Name
Value
Description
HANA administrator
name
hdbadm /
<Master Password>
Additional user for HANA lifecycle management –
start/stop, administration functions, recovery.
Generic HANA DB
user
BPINST / Welcome1
Generic user that can be used to access HANA DB
Technical S/4HANA
user
SAPHANADB /
<Master Password>
Technical user for accessing HANA from the S/4HANA
server. Defined in /nDBACOCKPIT; HANA schema
SAPHANADB contains the S/4HANA data
System database (use
Multiple Containers → System DB
when adding it to your local HANA Studio, needed e.g.
for applying your own HANA DB license key)
Name
Value
Description
HANA DB system
SYSTEMDB
System ID of the HANA DB
HANA DB Instance
Number
02
Instance number of HANA DB
HANA SYSTEM user
name
SYSTEM /
<Master Password>
Standard HANA system user
HANA administrator
name
hdbadm /
<Master Password>
Additional user for HANA lifecycle management –
start/stop, administration functions, recovery.
Generic HANA DB
user
BPINST / Welcome1
Generic user that can be used to access HANA DB
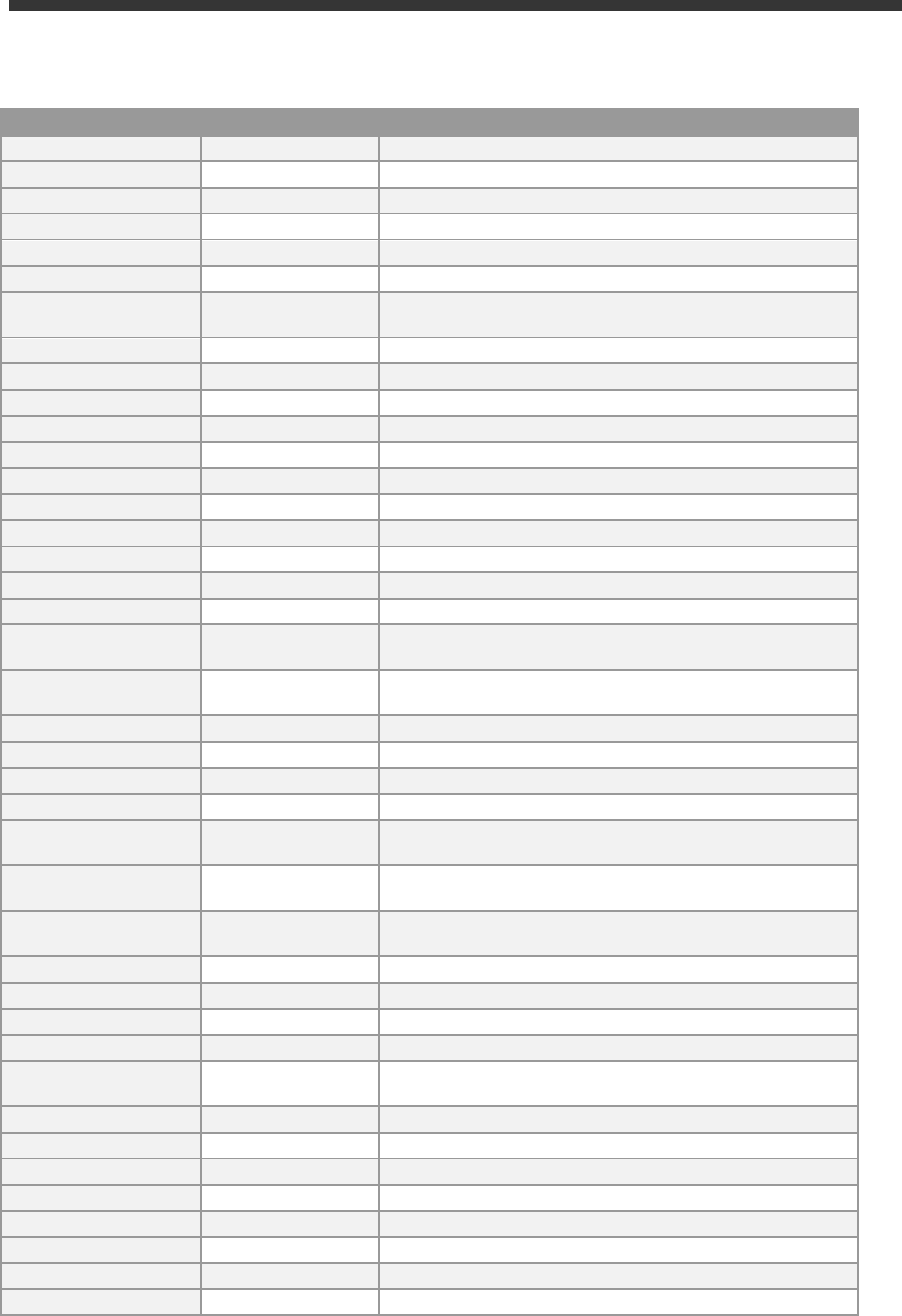
2.4.3 Java Application Server
Name
Value
Description
ASE administrator
name
sybadm /
<Master Password>
Additional user for Sybase ASE lifecycle management –
start/stop, administration.
JAVA administrator
name
Administrator /
<Master Password>
Additional user for JAVA lifecycle management –
start/stop, administration, functions, recovery.
Access to SAP NetWeaver Administrator:
https://vhcalj2eci.dummy.nodomain:50001/nwa
Additional JAVA user
BPINST / Welcome1
Generic user in case other users are locked
18
2.4.4 SAP BusinessObjects BI platform
Parameter ID
Parameter Value
Note
Administrator name
Administrator / Welcome1
Use for all administrative functions of
the BI platform e.g. in CMC
BI Power User
BPINST / Welcome1
Use for BI Launchpad
SQL Anywhere DB user
dba / Appl1ance
Use to log on to the DB of the BI
platform on Linux backend stored under
/data/bobj/sqlanywhere/database
BI Platform Linux backend
user
bipadm /
<Master
Password>
In the logon screen (http://bihost:8080/BOE/BI), use
bihost:6400
as system and Enterprise authentication.
Usage of the
bihost
alias requires local host file mapping when using local PC access (see section 2.3). The
Windows remote desktop has the mapping pre-configured.
2.4.5 Windows Frontend Server Details
Connect to the Frontend server using the information in the table below.
SAP does not provide a separate MS Windows Terminal Server license as part of the appliance; hence, you can
connect with a maximum of two concurrent users (with different user IDs) at the same time. The
Administrator
account is pre-configured, and you may create additional user IDs in the local user administration of the remote
desktop if needed.
If you want to use the remote desktop with larger user numbers, please apply your own MS Terminal Server
license to the remote desktop and potentially choose a larger sizing for the RDP in the CAL console.
Name
Value
Description
IP Address
<IP Address>
The IP address of your frontend server instance you
created in SAP CAL (use the “external” IP address)
User
Administrator /
<Master Password>
User for the Windows frontend server. This is a local user
on the remote desktop. Only one Administrator user can
logon to the front-end server at the same point in time.
A note on browsers:
Google Chrome and Firefox are pre-installed on the Remote Desktop. In the Fiori launchpad, you might find
slightly different rendering behaviors depending on the browser version. If you encounter rendering problems,
please search for SAP Notes how to potentially fix them.
If you want to access the Fiori Launchpad with a local browser, please be sure to map your local host file as
described in section 2.3 of this document or on https://www.sap.com/cmp/oth/crm-s4hana/s4hana-on-
19
premise.html
→ Quick Start Guide
since otherwise some Fiori applications (e.g. WebGUI or Web Dynpro) will not
work correctly.
2.4.6 Accessing Your Instance on Linux Level
You can access the Linux backend system of your appliance (ABAP / JAVA / BI) as
root
using secure SSH tools,
e.g. PuTTY
For information how to access a solution on OS level, go to this FAQ page and look under the question: How to
connect to a running instance via the secure shell protocol (SSH)?
Parameter ID
Parameter Value
Note
OS User Name
root
The default Linux administrator user
OS Password
<none>
Use the generated private key with SSH tools
Note:
You must use the private key (file format .pem) that was generated in the last step of the Create Instance wizard
from SAP Cloud Appliance Library. During the creation, you were asked to either store the key file attached to
your instance within SAP CAL or download it to a local secure file share on your computer.
Optional:
Get your own fully-qualified domain name & SSL certificate
The SAP S/4HANA Fully-Activated Appliance by default contains these two settings:
• A dummy domain name for Fiori access (*.dummy.nodomain)
• A certificate self-signed by SAP (issuer cal.dummy.nodomain)
Depending on network setup and end-user authorizations, these settings may cause problems:
• Business users need to change the
/etc/hosts
file with administrator rights on their PC (often not allowed)
• The corporate proxy or the end-user web browser might generally not trust self-signed certificates and
bounces them back
• Inbound connectivity into the S/4HANA system (e.g. from SAP Analytics Cloud) is not trusted due to a self-
signed certificate
On the demo guide blog of the appliance, you can find a technical guide how to enable this for your system.
The Fiori domain name change requires on SAP GUI access, and will take ~ 15 minutes.
The SSL certificate requires access to the Linux OS and basic Linux skills, and will take ~ 45 minutes.
Please be aware that the mentioned guide is meant to provide a quick workaround and might not comply with the
security recommendations that are issued by SAP in general.
20
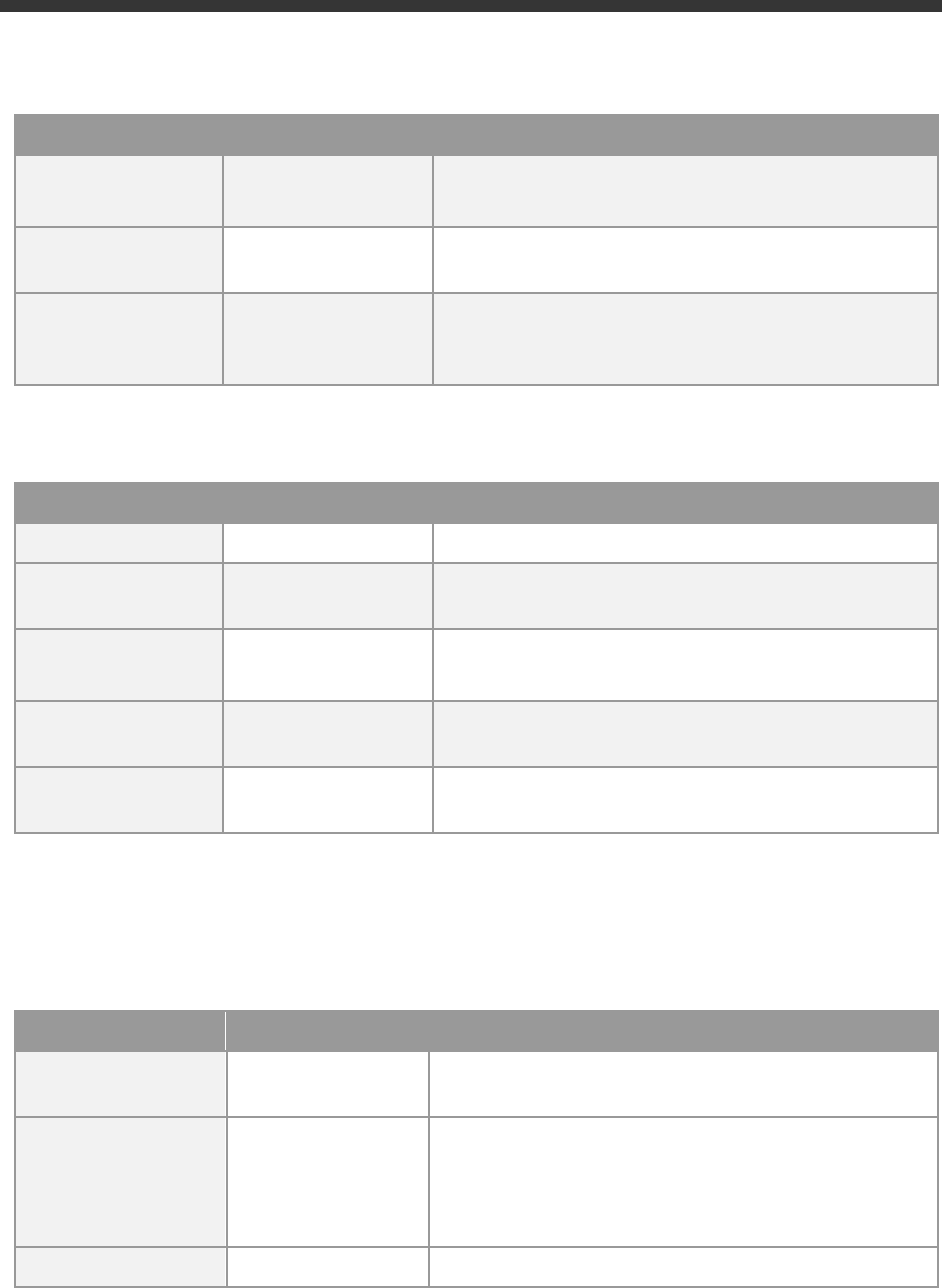
3 Licenses & Fees
SAP CAL is a platform for quickly using SAP on-premise software products in a hyperscaler environment.
Therefore, three separate license / cost factors need to be considered, each depending on the duration that your
system should be used:
a) the SAP on-premise product (e.g. SAP S/4HANA)
b) SAP Cloud Appliance Library
c) the chosen cloud provider
This table gives an overview about the different aspects. Details are mentioned in the paragraphs afterwards.
The third column in the table below (on-premise installation) is an alternative to SAP CAL and not covered in detail
in this document (please see SAP Note 2041140 for details).

21
First 30 days: Running your system instance as trial
In the first 30 days, the SAP license fees (CAL & S/4HANA) are waived. During this period, you only need to bear
the hosting fees of your cloud provider.
The 30-day period starts when you accept the form for the trial agreement in the CAL console (after clicking on
“Create Instance”).
During the instantiation, the S/4HANA system will generate a temporary license key that is enough for exploration
purposes.
Beyond 30 days: Running your instance with SAP licenses
If you want to use an appliance beyond the 30-day trial period (i.e. unlock the solution in SAP CAL), you need to
obtain two SAP licenses:
1. The SAP Cloud Appliance Library (SAP CAL) subscription
2. The SAP product licenses for the product(s) that are bundled within your appliance
The validity of these licenses will be automatically checked after the first 30 days. In case of a missing license
component an error message will be displayed in the SAP CAL console and the respective solution will stay in
status “Suspended”.
The cloud provider fees will stay the same as during the first 30 days.
You can continue to use a trial instance from the first 30 days under these conditions, all your changes in that
instance will be preserved once you unlock the solution.
3.2.1 SAP CAL subscription
You can purchase the subscription package via the SAP Store on
https://www.sapstore.com/solutions/99007/SAP-Cloud-Appliance-Library.
The minimum subscription is 3 months for one instance (i.e. you can have exactly one instance active at a time
during these 3 months). You can also choose longer subscription periods and higher instance numbers (i.e. you
can activate multiple solutions in parallel).
In the SAP Store, you will need an S-user that has the “SAP Store buyer role” assigned.
Please make sure that the SAP Store user and the SAP CAL user belong to the same organization, otherwise the
mapping between the license and the to-be-unlocked instance is not possible. In case these two users do now
belong to the same organization, please see this blog how to resolve this.

22
3.2.2 SAP product licenses
3.2.2.1 SAP S/4HANA Enterprise Mgmt. & SAP HANA DB
To use an instance under your own SAP Product License Agreements, you need to possess at least a license for
the SAP HANA DB (application runtime) and for SAP S/4HANA Enterprise Management professional use.
If you don’t possess these licenses already, you can either obtain them via your SAP account executive, or online
as self-service by licensing the free SAP S/4HANA 90-day trial in SAP Store.
The CAL infrastructure checks whether the customer/partner organization of the S-user who created the
instance in SAP CAL possesses these licenses. Only if this check is passed, the instance can be activated in SAP
CAL.
The licenses entitle your organization to use the appliance, however, since technically you will still be running
under the 90-day temporary license key, we recommend generating your own license key and apply it to your
system as soon as possible. 90 days after the initial instance creation, the system will stop working without these
technical license keys (see the next chapter for details).
Note:
The following separately licensed SAP S/4HANA capabilities are also configured and described in the pre-
configured demo scenarios of the appliance. These capabilities will technically work in your instance without
entering dedicated license keys for them, however, they might not be part of your customer-specific license
agreement for implementation / production systems.
• SAP S/4HANA Finance for cash mgmt.
• SAP S/4HANA Finance for receivables mgmt.
• SAP S/4HANA for advanced compliance reporting
• SAP Business Planning and Consolidation, add-on for S/4HANA
• SAP S/4HANA for extended planning
• SAP S/4HANA Advanced Available-to-Promise
• SAP S/4HANA for Advanced Variant Configuration, standard
• SAP Portfolio and Project Management for SAP S/4HANA professional
• SAP Enterprise Master Data Governance for SAP S/4HANA
3.2.2.2 Optional: SAP BusinessObjects BI Platform licenses
If you chose to use the optional SAP BusinessObjects Platform in your system instance, the temporary license key
for BI will be valid for 30 days. It needs to be replaced by your own permanent key for the BI platform after that
time if you want the BI platform to work.
If you don’t apply a permanent license key, the BI platform cannot be used anymore.
The other instance components (S/4HANA etc.) will not be affected and can be used even without the BI
platform.

23
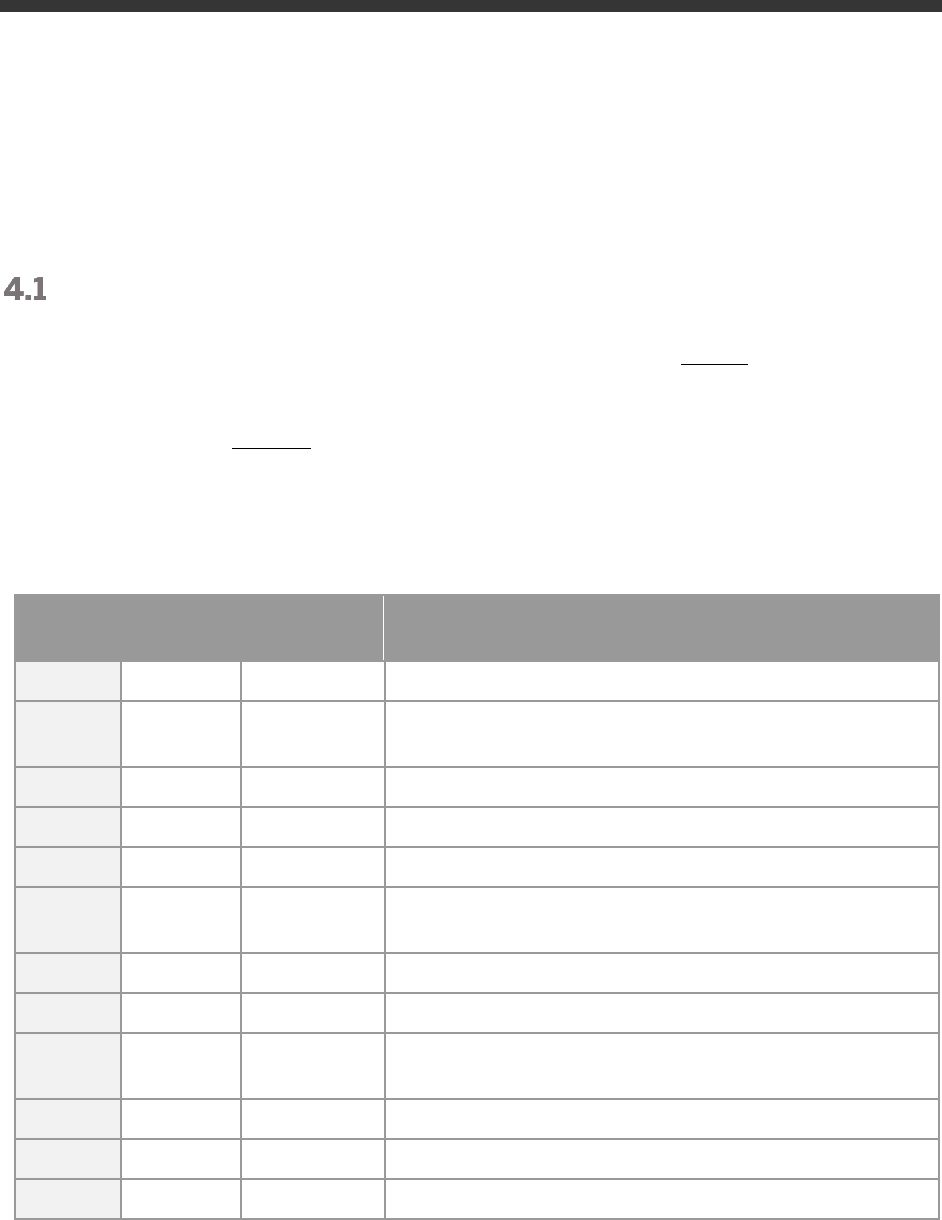
Beyond 90 days: License key installation required
Latest 90 days after instance creation (but better directly after unlocking the solution in CAL after 30 days), you
need to apply a valid license key to the system components.
• SAP S/4HANA
• SAP HANA database
• SAP NetWeaver J2EE platform
• Optional: SAP BusinessObjects BI platform
The first three are part of the SAP S/4HANA license; the BI platform needs to be licensed separately.
To get license keys for your system components, you first need to register them as a customer installation (see
https://support.sap.com/en/my-support/systems-installations.html).
Afterwards you can request license keys via the SAP license key application
(https://support.sap.com/licensekey).
During the license key generation, you will be asked for certain parameters (hardware keys and other system
properties). The table below has the details.
For S/4HANA and JAVA, you can also choose to generate a
“Maintenance Certificate”
together with the license
key. The Maintenance Certificate is valid for 3 months and only needed for advanced system operations e.g. the
installation of add-ons or support packages. It doesn’t affect the system in general so you can decide whether to
take it or not. More details are here.
For more information about how to generate and install product license keys, please see:
a) This blog for an overview
b) Step-by-step video (using an SAP-internal license key but the principle is the same for customers &
partners)
SID
Product
Version
DB
OS
Comment
Where to get the hardware key and apply
the license key
HDB
SAP HANA,
platform edition
SAP HANA
2.0, platform
edition
-
Linux
License type: SAP In-
memory Appliance
platform
Quantity: 256 GB
Memory Volume
HANA Studio: log on to system DB with
SYSTEM user;
right-click on system
→
Properties → Licenses.
HANA Studio on remote desktop has pre-
configured entry for system DB.
In a local HANA Studio use host name
vhcalhdbdb or IP address of ABAP/JAVA
VM; instance number 02; multiple
containers > system database.
S4H
SAP S/4HANA
SAP
S/4HANA
2020
SAP
HANA
database
Linux
N/A
Log on to S/4HANA with SAP GUI and use
tCode
/nSLICENSE
J2E
SAP NetWeaver
SAP
NetWeaver
7.5
Sybase
ASE
Linux
As license type, select
'J2EE - Web AS JAVA'
https://vhcalj2eci.dummy.nodomain:500
01/nwa with Administrator user →
Configuration → Infrastructure →
Licenses.
24
SID
Product
Version
DB
OS
Comment
Where to get the hardware key and apply
the license key
BIP
Optional:
SAP
BusinessObjects
Business
Intelligence
platform
SAP
BusinessObje
cts Business
Intelligence
platform 4.2
-
Linux
Material:
Choose SAP BO BI
Platform (with fitting
license KPI e.g.
concurrent sessions
CS,…) and version XI 4.2
BOE CMC
(http://bihost:8080/BOE/CMC) →
Licenses
Note to SAP employees:
You can generate SAP-internal license keys (18 months validity) directly in the license key application without
having to register your system (just enter the hardware key and the needed parameters).
3.3.1 What to do if your temporary license key has expired
If you missed to install your own permanent license key before the temporary 90-day key has expired, your
system will stop working, hence, if you experience connectivity errors roughly three months after the instance
creation think of an expired license key in the first place.
The procedure is now a bit more difficult since you need to get to a fully-licensed HANA DB first before you can
install the S/4 license key, therefore follow these steps:
1. Apply the HANA DB license key as described above. When you log on to the HANA system DB with the
SYSTEM user, you will only have limited options (incl. some warning messages) but the license key
installation works as usual.
2. Restart the S/4HANA ABAP system. The easiest way is to use the Reboot button in the CAL console but
you can also do it on Linux OS level with the sapcontrol command.
3. When the S/4 instance is active again, apply the license key to S/4HANA as described above. You need
to do this in client 000 with the user SAP* / <Master_Password>. Afterwards, HANA and S/4HANA
should run as before.
4. Apply the JAVA server license key as described above within 30 minutes after a re-boot or activation of
the instance. After this period, the JAVA server will go down until the next reboot / re-activation.
5. For SAP BusinessObjects (temporary license key expires after 30 days), apply the license key as
described above (no special considerations).
25
4 Security Aspects in SAP CAL
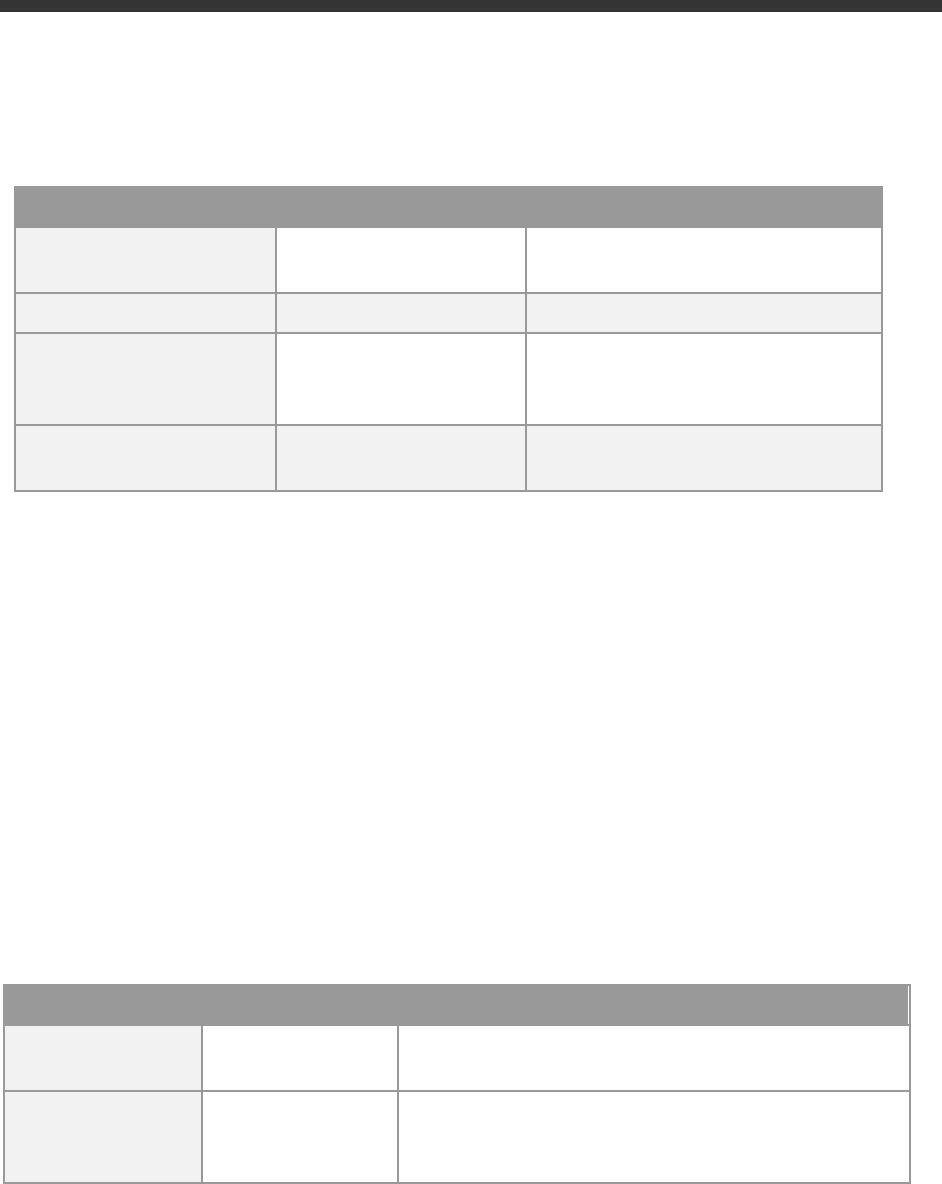
Internet ports for accessing your system
By default, the following ports are opened for your solution instance (i.e. this is the inbound firewall of your cloud
provider). The access from your local computer to your system instance happens via those ports (see
'Description' what port is used where).
Please make sure that your outbound firewall (e.g. if you are behind a corporate firewall) allows access through
the needed ports as well. If you encounter problems behind a firewall, a good test is to use a public network (e.g.
from home) or test access via the delivered remote desktop – assuming you can access the remote desktop via
port 3389.
You can edit/add/remove ports manually in the instance details (click on the instance link in the
CAL console →
Edit → Virtual Machine → Access Points
).
Virtual
Machine*
Protocol
Port (open by
default)
Description
ABAP
SSH
22
Used for secure connection to Linux-based server operating system
ABAP
HTTPS
44301, 44300
Used for access of a local web browser to appliance (Fiori etc.).
44301 via Web Dispatcher, 44300 via ABAP ICM directly
ABAP
HTTP
50000
Standard HTTP port for ABAP
ABAP
HTTPS
8443
Access to integrated Cloud Connector
ABAP
SAP GUI
3200
Used for access of local SAP GUI to appliance
ABAP
TCP
3300
Used for connection of ABAP Development Tools (Eclipse-based) to SAP
S/4HANA ABAP repository & RFC calls to other systems if intended
ABAP
TCP
30213 / 30215
Used for connection of SAP HANA Studio to HANA DB
JAVA
SSH
22
SSH connection to Linux operating system (e.g. for PuTTY)
JAVA
HTTPS
50001
Used for access to SAP NetWeaver Administrator and other web-based
J2EE applications
BIP
SSH
22
Used for secure connection to Linux-based server operating system
BIP
HTTP
8080 & 6400
Used for HTTP connection to BI platform
WIN
RDP
3389
Used for access from MS Windows remote desktop connection
* ABAP = SAP S/4HANA & SAP HANA DB;
JAVA = SAP NetWeaver 7.50 AS JAVA incl. ADS (Adobe Document Service)
BIP = SAP BusinessObjects BI Platform 4.2
WIN = MS Windows Remote Desktop
26
Network security considerations
Be aware that creating your instances in the public zone of your cloud provider (i.e. the “open Internet”) is
convenient but less secure than providing it within your corporate network.
If you want to tighten the security, open as few ports as really needed for your scenario.
In addition, we also recommend that you limit the access to your instances by defining a whitelisted IP range of IP
addresses that may access your solution (e.g. the subnet of your company). With this, only computers within the
white-listed IP range can access your system via the specific port. You can maintain the IP Range settings in the
CAL console
→ Edit → Virtual Machine → Access Points.
, using CIDR notation.
The more complex but also more secure alternative to public Internet is to set up a virtual private cloud (VPC) with
VPN access (e.g. described in this tutorial or in your standard cloud provider documentation).
Note that when using HANA based appliances, HANA systems are not installed individually but cloned from a
template system. Because of this cloning process, the existing root keys are cloned. For more information, see
this SAP Note 2134846 - HANA encryption key handling during system cloning.
ABAP user roles and profiles
The ABAP business users listed in chapter 2 have a large set of roles and extensive authorizations (including the
SAP_ALL profile).
If you plan to release the appliance to a larger set of users (especially in the Internet scenario), it is advised to
restrict/lock the access with these users (or change the initial passwords) and create your own users with fitting
roles and authorizations.
This can be done using the standard user management capabilities (e.g. tCode SU01, etc.).
Please also note that the user BPINST is used in various RFC connections (tCode SM59) with its fixed password. If
you lock the BPINST user or change its password, please also adapt these connections accordingly.
Certificates
The appliance comes with a certificate that was self-signed by SAP. Most local browsers will issue a warning
message that such a certificate is untrusted, and you will need to add the affected URLs (Fiori launchpad and
others) to the list of trusted sites once.
Hence, if you see messages about unsafe connections, untrusted certificates, etc., please click on “Proceed” or “I
know the risk”, etc. (the screens and needed clicks will vary depending on the browser).
As an alternative, you can also apply your own trusted certificate to the system (using tCode STRUST, etc.).
The above-mentioned sample demo walkthrough site provides a technical demo guide for installing a free 90-day
Let’s Encrypt certificate.
On the delivered remote desktop, the self-signed certificate has already been imported into the store with trusted
certificates, and you will not see a warning if you access the Fiori launchpad. The web sites of the J2EE server or
the SAP Cloud Connector will still display warnings, please acknowledge the risk and continue as outlined above.
27
5 Solution Provisioning in SAP Cloud
Appliance Library
If you have a user in SAP Cloud Appliance Library, you need to meet the following prerequisites before starting to
use the SAP Cloud Appliance library:
Cloud Provider Configurations
You have a valid account in one of the cloud providers supported by SAP Cloud Appliance Library. If you already
have an active cloud provider account, you can proceed directly with the next section. Otherwise, navigate to the
cloud provider home page and sign up.
For more information about the supported cloud providers, see the FAQ page or this YouTube playlist.
Navigate to SAP Cloud Appliance Library
Open the SAP Cloud Appliance Library in your Web browser using the following link: https://cal.sap.com
For more information about how to use solutions in SAP Cloud Appliance Library, see the official documentation
of SAP Cloud Appliance Library (choose Support → Documentation link and choose (expand all) button to see
all documents in the structure). You can also use the context help in SAP Cloud Appliance Library by choosing the
Help panel from the right side.
28
6 Appendix
Installed Technical Component Details
6.1.1 SAP ABAP application server 7.55 with SAP S/4HANA
2020 FPS01 & SAP HANA DB 2.0.54
Component
Release
SP-
Level
Support Package
Short Description of Component
SAP_BASIS
755
0001
SAPK-
75501INSAPBASIS
SAP Basis Component
SAP_ABA
75F
0001
SAPK-
75F01INSAPABA
Cross-Application Component
SAP_GWFND
755
0001
SAPK-
75501INSAPGWFND
SAP Gateway Foundation
SAP_UI
755
0002
SAPK-75502INSAPUI
User Interface Technology
ST-PI
740
0014
SAPK-74014INSTPI
SAP Solution Tools Plug-In
SAP_BW
755
0001
SAPK-75501INSAPBW
SAP Business Warehouse
UIBAS001
600
0001
SAPK-
60001INUIBAS001
UI for Basis Applications 6.0
MDG_FND
805
0001
SAPK-
80501INMDGFND
MDG Foundation
S4FND
105
0001
SAPK-10501INS4FND
Foundation
MDG_APPL
805
0001
SAPK-
80501INMDGAPPL
MDG Applications
S4CEXT
105
0001
SAPK-
10501INS4CEXT
S4CEXT
S4CORE
105
0001
SAPK-
10501INS4CORE
S4CORE
S4CRM
205
0001
SAPK-20501INS4CRM
S4CRM
SAP_HR
608
0087
SAPKE60887
Human Resources
SAP_HRCAE
608
0087
SAPK-
60887INSAPHRCAE
Subcomponent SAP_HRCAE of
SAP_HR
SAP_HRCAR
608
0087
SAPK-
60887INSAPHRCAR
Subcomponent SAP_HRCAR of
SAP_HR
SAP_HRCAT
608
0087
SAPK-
60887INSAPHRCAT
Subcomponent SAP_HRCAT of
SAP_HR
SAP_HRCAU
608
0087
SAPK-
60887INSAPHRCAU
Subcomponent SAP_HRCAU of
SAP_HR
SAP_HRCBE
608
0087
SAPK-
60887INSAPHRCBE
Subcomponent SAP_HRCBE of
SAP_HR
SAP_HRCBG
608
0087
SAPK-
60887INSAPHRCBG
Subcomponent SAP_HRCBG of
SAP_HR
29
Component
Release
SP-
Level
Support Package
Short Description of Component
SAP_HRCBR
608
0087
SAPK-
60887INSAPHRCBR
Subcomponent SAP_HRCBR of
SAP_HR
SAP_HRCCA
608
0087
SAPK-
60887INSAPHRCCA
Subcomponent SAP_HRCCA of
SAP_HR
SAP_HRCCH
608
0087
SAPK-
60887INSAPHRCCH
Subcomponent SAP_HRCCH of
SAP_HR
SAP_HRCCL
608
0087
SAPK-
60887INSAPHRCCL
Subcomponent SAP_HRCCL of
SAP_HR
SAP_HRCCN
608
0087
SAPK-
60887INSAPHRCCN
Subcomponent SAP_HRCCN of
SAP_HR
SAP_HRCCO
608
0087
SAPK-
60887INSAPHRCCO
Subcomponent SAP_HRCCO of
SAP_HR
SAP_HRCCZ
608
0087
SAPK-
60887INSAPHRCCZ
Subcomponent SAP_HRCCZ of
SAP_HR
SAP_HRCDE
608
0087
SAPK-
60887INSAPHRCDE
Subcomponent SAP_HRCDE of
SAP_HR
SAP_HRCDK
608
0087
SAPK-
60887INSAPHRCDK
Subcomponent SAP_HRCDK of
SAP_HR
SAP_HRCEG
608
0087
SAPK-
60887INSAPHRCEG
Subcomponent SAP_HRCEG of
SAP_HR
SAP_HRCES
608
0087
SAPK-
60887INSAPHRCES
Subcomponent SAP_HRCES of
SAP_HR
SAP_HRCFI
608
0087
SAPK-
60887INSAPHRCFI
Subcomponent SAP_HRCFI of
SAP_HR
SAP_HRCFR
608
0087
SAPK-
60887INSAPHRCFR
Subcomponent SAP_HRCFR of
SAP_HR
SAP_HRCGB
608
0087
SAPK-
60887INSAPHRCGB
Subcomponent SAP_HRCGB of
SAP_HR
SAP_HRCGR
608
0087
SAPK-
60887INSAPHRCGR
Subcomponent SAP_HRCGR of
SAP_HR
SAP_HRCHK
608
0087
SAPK-
60887INSAPHRCHK
Subcomponent SAP_HRCHK of
SAP_HR
SAP_HRCHR
608
0087
SAPK-
60887INSAPHRCHR
Subcomponent SAP_HRCHR of
SAP_HR
SAP_HRCHU
608
0087
SAPK-
60887INSAPHRCHU
Subcomponent SAP_HRCHU of
SAP_HR
SAP_HRCID
608
0087
SAPK-
60887INSAPHRCID
Subcomponent SAP_HRCID of
SAP_HR
SAP_HRCIE
608
0087
SAPK-
60887INSAPHRCIE
Subcomponent SAP_HRCIE of
SAP_HR
SAP_HRCIN
608
0087
SAPK-
60887INSAPHRCIN
Subcomponent SAP_HRCIN of
SAP_HR
SAP_HRCIT
608
0087
SAPK-
60887INSAPHRCIT
Subcomponent SAP_HRCIT of
SAP_HR
SAP_HRCJP
608
0087
SAPK-
60887INSAPHRCJP
Subcomponent SAP_HRCJP of
SAP_HR
SAP_HRCKR
608
0087
SAPK-
60887INSAPHRCKR
Subcomponent SAP_HRCKR of
SAP_HR
SAP_HRCKW
608
0087
SAPK-
60887INSAPHRCKW
Subcomponent SAP_HRCKW of
SAP_HR
SAP_HRCKZ
608
0087
SAPK-
60887INSAPHRCKZ
Subcomponent SAP_HRCKZ of
SAP_HR
30
Component
Release
SP-
Level
Support Package
Short Description of Component
SAP_HRCMX
608
0087
SAPK-
60887INSAPHRCMX
Subcomponent SAP_HRCMX of
SAP_HR
SAP_HRCMY
608
0087
SAPK-
60887INSAPHRCMY
Subcomponent SAP_HRCMY of
SAP_HR
SAP_HRCNL
608
0087
SAPK-
60887INSAPHRCNL
Subcomponent SAP_HRCNL of
SAP_HR
SAP_HRCNO
608
0087
SAPK-
60887INSAPHRCNO
Subcomponent SAP_HRCNO of
SAP_HR
SAP_HRCNZ
608
0087
SAPK-
60887INSAPHRCNZ
Subcomponent SAP_HRCNZ of
SAP_HR
SAP_HRCOM
608
0087
SAPK-
60887INSAPHRCOM
Subcomponent SAP_HRCOM of
SAP_HR
SAP_HRCPH
608
0087
SAPK-
60887INSAPHRCPH
Subcomponent SAP_HRCPH of
SAP_HR
SAP_HRCPL
608
0087
SAPK-
60887INSAPHRCPL
Subcomponent SAP_HRCPL of
SAP_HR
SAP_HRCPT
608
0087
SAPK-
60887INSAPHRCPT
Subcomponent SAP_HRCPT of
SAP_HR
SAP_HRCQA
608
0087
SAPK-
60887INSAPHRCQA
Subcomponent SAP_HRCQA of
SAP_HR
SAP_HRCRO
608
0087
SAPK-
60887INSAPHRCRO
Subcomponent SAP_HRCRO of
SAP_HR
SAP_HRCRU
608
0087
SAPK-
60887INSAPHRCRU
Subcomponent SAP_HRCRU of
SAP_HR
SAP_HRCSA
608
0087
SAPK-
60887INSAPHRCSA
Subcomponent SAP_HRCSA of
SAP_HR
SAP_HRCSE
608
0087
SAPK-
60887INSAPHRCSE
Subcomponent SAP_HRCSE of
SAP_HR
SAP_HRCSG
608
0087
SAPK-
60887INSAPHRCSG
Subcomponent SAP_HRCSG of
SAP_HR
SAP_HRCSI
608
0087
SAPK-
60887INSAPHRCSI
Subcomponent SAP_HRCSI of
SAP_HR
SAP_HRCSK
608
0087
SAPK-
60887INSAPHRCSK
Subcomponent SAP_HRCSK of
SAP_HR
SAP_HRCTH
608
0087
SAPK-
60887INSAPHRCTH
Subcomponent SAP_HRCTH of
SAP_HR
SAP_HRCTR
608
0087
SAPK-
60887INSAPHRCTR
Subcomponent SAP_HRCTR of
SAP_HR
SAP_HRCTW
608
0087
SAPK-
60887INSAPHRCTW
Subcomponent SAP_HRCTW of
SAP_HR
SAP_HRCUA
608
0087
SAPK-
60887INSAPHRCUA
Subcomponent SAP_HRCUA of
SAP_HR
SAP_HRCUN
608
0087
SAPK-
60887INSAPHRCUN
Subcomponent SAP_HRCUN of
SAP_HR
SAP_HRCUS
608
0087
SAPK-
60887INSAPHRCUS
Subcomponent SAP_HRCUS of
SAP_HR
SAP_HRCVE
608
0087
SAPK-
60887INSAPHRCVE
Subcomponent SAP_HRCVE of
SAP_HR
SAP_HRCZA
608
0087
SAPK-
60887INSAPHRCZA
Subcomponent SAP_HRCZA of
SAP_HR
SAP_HRGXX
608
0087
SAPK-
60887INSAPHRGXX
Subcomponent SAP_HRGXX of
SAP_HR
31
Component
Release
SP-
Level
Support Package
Short Description of Component
SAP_HRRXX
608
0087
SAPK-
60887INSAPHRRXX
Subcomponent SAP_HRRXX of
SAP_HR
EA-DFPS
805
0001
SAPK-
80501INEADFPS
SAP Enterprise Extension Defense
Forces & Public Security
EA-HR
608
0087
SAPK-60887INEAHR
SAP Enterprise Extension HR
EA-HRCAE
608
0087
SAPK-
60887INEAHRCAE
Subcomponent EA-HRCAE of EA-
HR
EA-HRCAR
608
0087
SAPK-
60887INEAHRCAR
Subcomponent EA-HRCAR of EA-
HR
EA-HRCAT
608
0087
SAPK-
60887INEAHRCAT
Subcomponent EA-HRCAT of EA-
HR
EA-HRCAU
608
0087
SAPK-
60887INEAHRCAU
Subcomponent EA-HRCAU of EA-
HR
EA-HRCBE
608
0087
SAPK-
60887INEAHRCBE
Subcomponent EA-HRCBE of EA-
HR
EA-HRCBG
608
0087
SAPK-
60887INEAHRCBG
Subcomponent EA-HRCBG of EA-
HR
EA-HRCBR
608
0087
SAPK-
60887INEAHRCBR
Subcomponent EA-HRCBR of EA-
HR
EA-HRCCA
608
0087
SAPK-
60887INEAHRCCA
Subcomponent EA-HRCCA of EA-
HR
EA-HRCCH
608
0087
SAPK-
60887INEAHRCCH
Subcomponent EA-HRCCH of EA-
HR
EA-HRCCL
608
0087
SAPK-
60887INEAHRCCL
Subcomponent EA-HRCCL of EA-
HR
EA-HRCCN
608
0087
SAPK-
60887INEAHRCCN
Subcomponent EA-HRCCN of EA-
HR
EA-HRCCO
608
0087
SAPK-
60887INEAHRCCO
Subcomponent EA-HRCCO of EA-
HR
EA-HRCCZ
608
0087
SAPK-
60887INEAHRCCZ
Subcomponent EA-HRCCZ of EA-
HR
EA-HRCDE
608
0087
SAPK-
60887INEAHRCDE
Subcomponent EA-HRCDE of EA-
HR
EA-HRCDK
608
0087
SAPK-
60887INEAHRCDK
Subcomponent EA-HRCDK of EA-
HR
EA-HRCEG
608
0087
SAPK-
60887INEAHRCEG
Sub component EA-HRCEG of EA-
HR
EA-HRCES
608
0087
SAPK-
60887INEAHRCES
Subcomponent EA-HRCES of EA-
HR
EA-HRCFI
608
0087
SAPK-
60887INEAHRCFI
Subcomponent EA-HRCFI of EA-HR
EA-HRCFR
608
0087
SAPK-
60887INEAHRCFR
Subcomponent EA-HRCFR of EA-
HR
EA-HRCGB
608
0087
SAPK-
60887INEAHRCGB
Subcomponent EA-HRCGB of EA-
HR
EA-HRCGR
608
0087
SAPK-
60887INEAHRCGR
Subcomponent EA-HRCGR of EA-
HR
EA-HRCHK
608
0087
SAPK-
60887INEAHRCHK
Subcomponent EA-HRCHK of EA-
HR
EA-HRCHR
608
0087
SAPK-
60887INEAHRCHR
Subcomponent EA-HRCHR of EA-
HR
32
Component
Release
SP-
Level
Support Package
Short Description of Component
EA-HRCHU
608
0087
SAPK-
60887INEAHRCHU
Subcomponent EA-HRCHU of EA-
HR
EA-HRCID
608
0087
SAPK-
60887INEAHRCID
Subcomponent EA-HRCID of EA-HR
EA-HRCIE
608
0087
SAPK-
60887INEAHRCIE
Subcomponent EA-HRCIE of EA-HR
EA-HRCIN
608
0087
SAPK-
60887INEAHRCIN
Subcomponent EA-HRCIN of EA-HR
EA-HRCIT
608
0087
SAPK-
60887INEAHRCIT
Subcomponent EA-HRCIT of EA-HR
EA-HRCJP
608
0087
SAPK-
60887INEAHRCJP
Subcomponent EA-HRCJP of EA-
HR
EA-HRCKR
608
0087
SAPK-
60887INEAHRCKR
Subcomponent EA-HRCKR of EA-
HR
EA-HRCKW
608
0087
SAPK-
60887INEAHRCKW
Subcomponent EA-HRCKW of EA-
HR
EA-HRCKZ
608
0087
SAPK-
60887INEAHRCKZ
Subcomponent EA-HRCKZ of EA-
HR
EA-HRCMX
608
0087
SAPK-
60887INEAHRCMX
Subcomponent EA-HRCMX of EA-
HR
EA-HRCMY
608
0087
SAPK-
60887INEAHRCMY
Subcomponent EA-HRCMY of EA-
HR
EA-HRCNL
608
0087
SAPK-
60887INEAHRCNL
Subcomponent EA-HRCNL of EA-
HR
EA-HRCNO
608
0087
SAPK-
60887INEAHRCNO
Subcomponent EA-HRCNO of EA-
HR
EA-HRCNZ
608
0087
SAPK-
60887INEAHRCNZ
Subcomponent EA-HRCNZ of EA-
HR
EA-HRCOM
608
0087
SAPK-
60887INEAHRCOM
Subcomponent EA-HRCOM of EA-
HR
EA-HRCPH
608
0087
SAPK-
60887INEAHRCPH
Subcomponent EA-HRCPH of EA-
HR
EA-HRCPL
608
0087
SAPK-
60887INEAHRCPL
Subcomponent EA-HRCPL of EA-
HR
EA-HRCPT
608
0087
SAPK-
60887INEAHRCPT
Subcomponent EA-HRCPT of EA-
HR
EA-HRCQA
608
0087
SAPK-
60887INEAHRCQA
Subcomponent EA-HRCQA of EA-
HR
EA-HRCRO
608
0087
SAPK-
60887INEAHRCRO
Subcomponent EA-HRCRO of EA-
HR
EA-HRCRU
608
0087
SAPK-
60887INEAHRCRU
Subcomponent EA-HRCRU of EA-
HR
EA-HRCSA
608
0087
SAPK-
60887INEAHRCSA
Subcomponent EA-HRCSA of EA-
HR
EA-HRCSE
608
0087
SAPK-
60887INEAHRCSE
Subcomponent EA-HRCSE of EA-
HR
EA-HRCSG
608
0087
SAPK-
60887INEAHRCSG
Subcomponent EA-HRCSG of EA-
HR
EA-HRCSI
608
0087
SAPK-
60887INEAHRCSI
Subcomponent EA-HRCSI of EA-HR
EA-HRCSK
608
0087
SAPK-
60887INEAHRCSK
Subcomponent EA-HRCSK of EA-
HR
33
Component
Release
SP-
Level
Support Package
Short Description of Component
EA-HRCTH
608
0087
SAPK-
60887INEAHRCTH
Subcomponent EA-HRCTH of EA-
HR
EA-HRCTR
608
0087
SAPK-
60887INEAHRCTR
Subcomponent EA-HRCTR of EA-
HR
EA-HRCTW
608
0087
SAPK-
60887INEAHRCTW
Subcomponent EA-HRCTW of EA-
HR
EA-HRCUA
608
0087
SAPK-
60887INEAHRCUA
Subcomponent EA-HRCUA of EA-
HR
EA-HRCUN
608
0087
SAPK-
60887INEAHRCUN
Subcomponent EA-HRCUN of EA-
HR
EA-HRCUS
608
0087
SAPK-
60887INEAHRCUS
Subcomponent EA-HRCUS of EA-
HR
EA-HRCVE
608
0087
SAPK-
60887INEAHRCVE
Subcomponent EA-HRCVE of EA-
HR
EA-HRCZA
608
0087
SAPK-
60887INEAHRCZA
Subcomponent EA-HRCZA of EA-
HR
EA-HRGXX
608
0087
SAPK-
60887INEAHRGXX
Subcomponent EA-HRGXX of EA-
HR
EA-HRRXX
608
0087
SAPK-
60887INEAHRRXX
Subcomponent EA-HRRXX of EA-
HR
EA-PS
805
0001
SAPK-80501INEAPS
SAP Enterprise Extension Public
Services
FI-CAX
805
0001
SAPK-80501INFICAX
FI-CA Extended
INSURANCE
805
0001
SAPK-
80501ININSURANC
SAP Insurance
IS-OIL
805
0001
SAPK-80501INISOIL
IS-OIL
IS-PRA
805
0001
SAPK-80501INISPRA
SAP IS-PRA
IS-PS-CA
805
0001
SAPK-80501INISPSCA
IS-PUBLIC SECTOR CONTRACT
ACCOUNTING
IS-UT
805
0001
SAPK-80501INISUT
SAP Utilities/Telecommunication
S4COREOP
105
0001
SAPK-
10501INS4COREOP
S/4HANA, On-Premise only parts
S4DEPREC
105
0000
-
S/4HANA, deprecation parts
GBX01HR
600
0019
SAPK-
60019INGBX01HR
FIORI X1 HCM
GBX01HR5
605
0016
SAPK-
60516INGBX01HR5
FIORI X1 HCM
SRA004
600
0011
SAPK-60011INSRA004
Create Travel Request OData
Integration
UIAPFI70
800
0001
SAPK-
80001INUIAPFI70
UI SFIN
UIHR001
100
0018
SAPK-
10018INUIHR001
UI for ERP Human Capital
Management
UIHR002
100
0012
SAPK-
10012INUIHR002
UI for ERP Human Capital
Management 100
UIS4HOP1
600
0001
SAPK-
60001INUIS4HOP1
UI for S/4HANA On Premise
PERSONAS
300
0012
SAPK-
30012INPERSONAS
PERSONAS - SAP GUI
PERSONALISATION
ST-A/PI
01U_731
0000
-
Servicetools for SAP Basis 731 and
higher
34
6.1.2 SAP HANA Database Plug-In Versions
HANA Version is
2.00.054.00.1611906357 (fa/hana2sp05)
Plug-in
Key
Value
AFL
HANA auxversion
0000.00.0
AFL
HANA changeinfo
CONT
989e98fd1334a1b6e36785c8bd7e9ab5239960f1
(fa/hana2sp05)
AFL
HANA
cloud_edition
0000.00.00
AFL
HANA
compilebranch
fa/hana2sp05
AFL
HANA compiler-
version-full
gcc (SAP release 20200227, based on SUSE gcc9-
9.2.1+r275327-1.3.7) 9.2.1 20190903 [gcc-9-branch
revision 275330]
AFL
HANA
compiletype
rel
AFL
HANA date
29.01.2021 08:49
AFL
HANA fullversion
2.00.054.00 Build 1611906357-1530
AFL
HANA git-hash
989e98fd1334a1b6e36785c8bd7e9ab5239960f1
AFL
HANA git-
headcount
500020
AFL
HANA git-
mergeepoch
1611906357
AFL
HANA git-
mergetime
29.01.2021 08:45
AFL
HANA hdb-state
RAMP
AFL
HANA makeid
8370882
AFL
HANA rev-
changelist
1611906357
AFL
HANA rev-
patchlevel
0
AFL
HANA sapexe-
branch
753_REL
AFL
HANA sapexe-
changelist
2007209
AFL
HANA sapexe-
version
753
AFL
HANA sp-
patchlevel
0
AFL
PPMS-SP-Level
54
AFL
PPMS-SP-Patch-
Level
0
AFL
PPMS-Technical-
Name
HANA_AFL
AFL
PPMS-Technical-
Release
2.0
AFL
afl-state
RAMP
35
Plug-in
Key
Value
AFL
changeinfo
CONT
9ce1799fc4f949856d57dac71e1da498972d676f
(fa/afl2sp05)
AFL
compilebranch
fa/afl2sp05
AFL
compiler-version
GCC 9
AFL
compiler-version-
full
gcc (SAP release 20200227, based on SUSE gcc9-
9.2.1+r275327-1.3.7) 9.2.1 20190903 [gcc-9-branch
revision 275330]
AFL
compiletype
rel
AFL
component-key
afl
AFL
compversion-id
7,35549E+19
AFL
date
29.01.2021 15:09
AFL
fullversion
2.00.054.0000 Build 1611928859-1530
AFL
git-hash
9ce1799fc4f949856d57dac71e1da498972d676f
AFL
git-headcount
45
AFL
git-mergeepoch
1611928859
AFL
git-mergetime
29.01.2021 15:00
AFL
keycaption
SAP HANA AFL (incl.PAL,BFL,OFL)
AFL
keyname
HANA_AFL
AFL
keyvendor
sap.com
AFL
makeid
8372578
AFL
ofl-version
13. Sep
AFL
platform
linuxx86_64
AFL
release
2.00
AFL
required-
components
name="HDB"; vendor="sap.com"
AFL
rev-changelist
1611928859
AFL
rev-number
54
AFL
rev-patchlevel
0
AFL
server-plugin
1
AFL
sp-number
54
AFL
sp-patchlevel
0
LCAPPS
HANA auxversion
0000.00.0
LCAPPS
HANA changeinfo
CONT
989e98fd1334a1b6e36785c8bd7e9ab5239960f1
(fa/hana2sp05)
LCAPPS
HANA
compilebranch
fa/hana2sp05
LCAPPS
HANA compiler-
version-full
gcc (SAP release 20200227, based on SUSE gcc9-
9.2.1+r275327-1.3.7) 9.2.1 20190903 [gcc-9-branch
revision 275330]
LCAPPS
HANA
compiletype
rel
LCAPPS
HANA date
29.01.2021 08:49
LCAPPS
HANA fullversion
2.00.054.00 Build 1611906357-1530
LCAPPS
HANA git-hash
989e98fd1334a1b6e36785c8bd7e9ab5239960f1
LCAPPS
HANA git-
headcount
500020
36
Plug-in
Key
Value
LCAPPS
HANA git-
mergeepoch
1611906357
LCAPPS
HANA git-
mergetime
29.01.2021 08:45
LCAPPS
HANA makeid
8370882
LCAPPS
HANA rev-
changelist
1611906357
LCAPPS
HANA rev-
patchlevel
0
LCAPPS
HANA sapexe-
branch
753_REL
LCAPPS
HANA sapexe-
changelist
2007209
LCAPPS
HANA sapexe-
version
753
LCAPPS
HANA sp-
patchlevel
0
LCAPPS
LCAPPS branch
10.0_REL
LCAPPS
LCAPPS build
47
LCAPPS
LCAPPS compiler
info
/LCAPPS/100_REL/20newdb/linuxx86_64/genopt/hm/
c/dependencies/lcapps/gcc-9.2.1+r275327-
1.3.7.sap20200227-linuxx86_64-linuxx86_64/bin/g++
LCAPPS
LCAPPS make
date
Fri 29 Jan 2021 04:15:49 PM CET
LCAPPS
LCAPPS patch
level
5
LCAPPS
LCAPPS release
10.00
LCAPPS
LCAPPS technical
version
LC_200054_64_RAMP/004 sp-pl 0000 Build 504199-
10.00COM047.5-10.0_REL-rel
LCAPPS
PPMS-SP-Level
2054
LCAPPS
PPMS-SP-Patch-
Level
0
LCAPPS
PPMS-Technical-
Name
LCAPPS_HDB
LCAPPS
PPMS-Technical-
Release
1.00
LCAPPS
compiletype
rel
LCAPPS
component-key
lcapps
LCAPPS
compversion-id
6,78378E+19
LCAPPS
fullversion
2.00.054.0000.504199
LCAPPS
keycaption
SAP HANA LCAPPS
LCAPPS
keyname
LCAPPS_HDB
LCAPPS
keyvendor
sap.com
LCAPPS
makeid
5733839
LCAPPS
platform
linuxx86_64
LCAPPS
release
2.00
LCAPPS
required-
components
name="HDB"; vendor="sap.com";
version="[2.00.054.00.1611906357,2.00.054.00.1611
906357]"
LCAPPS
rev-changelist
504199
37
Plug-in
Key
Value
LCAPPS
rev-number
54
LCAPPS
rev-patchlevel
0
LCAPPS
server-plugin
1
LCAPPS
sp-number
2054
LCAPPS
sp-patchlevel
0
SAP_AFL_SDK_APL
auxversion
0000.00.0
SAP_AFL_SDK_APL
changeinfo
CONT dd499ff01d3137f1a61ccb15ed34a9a7ea3b5dbf
(fa/hana1sp12)
SAP_AFL_SDK_APL
compilebranch
undefined
SAP_AFL_SDK_APL
compilebranch
fa/hana1sp12
SAP_AFL_SDK_APL
compiletype
rel
SAP_AFL_SDK_APL
component-key
sap_afl_sdk_apl
SAP_AFL_SDK_APL
compversion-id
7,35549E+19
SAP_AFL_SDK_APL
date
06.03.2020 17:20
SAP_AFL_SDK_APL
fullversion
4.203.2008.0
SAP_AFL_SDK_APL
git-hash
dd499ff01d3137f1a61ccb15ed34a9a7ea3b5dbf
SAP_AFL_SDK_APL
git-headcount
500031
SAP_AFL_SDK_APL
git-mergeepoch
1478575636
SAP_AFL_SDK_APL
git-mergetime
08.11.2016 04:27
SAP_AFL_SDK_APL
hana_afl_sdk-
major-version
2
SAP_AFL_SDK_APL
hana_afl_sdk-
minor-version
13
SAP_AFL_SDK_APL
hdb-state
RAMP
SAP_AFL_SDK_APL
keycaption
Automated Predictive Library
SAP_AFL_SDK_APL
keyname
sap_afl_sdk_apl
SAP_AFL_SDK_APL
keyvendor
sap.com
SAP_AFL_SDK_APL
lcmsdk-major-
version
2
SAP_AFL_SDK_APL
lcmsdk-minor-
version
5
SAP_AFL_SDK_APL
lcmsdk-patch-
version
26
SAP_AFL_SDK_APL
lcmsdk-version
02.05.2026
SAP_AFL_SDK_APL
makeid
1
SAP_AFL_SDK_APL
platform
linuxx86_64
SAP_AFL_SDK_APL
release
4.203
SAP_AFL_SDK_APL
required-
components
name="HDB"; vendor="sap.com";
version="[2.00.030.0,9999.9999.9999.9999)"
SAP_AFL_SDK_APL
rev-changelist
0
SAP_AFL_SDK_APL
rev-number
2008
SAP_AFL_SDK_APL
rev-patchlevel
0
SAP_AFL_SDK_APL
sapexe-branch
745_REL
SAP_AFL_SDK_APL
sapexe-changelist
1711525
SAP_AFL_SDK_APL
sapexe-version
745
SAP_AFL_SDK_APL
server-plugin
1
VCH2020
HANA auxversion
0000.00.0
38
Plug-in
Key
Value
VCH2020
HANA changeinfo
CONT
989e98fd1334a1b6e36785c8bd7e9ab5239960f1
(fa/hana2sp05)
VCH2020
HANA
cloud_edition
0000.00.00
VCH2020
HANA
compilebranch
fa/hana2sp05
VCH2020
HANA compiler-
version-full
gcc (SAP release 20200227, based on SUSE gcc9-
9.2.1+r275327-1.3.7) 9.2.1 20190903 [gcc-9-branch
revision 275330]
VCH2020
HANA
compiletype
rel
VCH2020
HANA date
29.01.2021 08:49
VCH2020
HANA fullversion
2.00.054.00 Build 1611906357-1530
VCH2020
HANA git-hash
989e98fd1334a1b6e36785c8bd7e9ab5239960f1
VCH2020
HANA git-
headcount
500020
VCH2020
HANA git-
mergeepoch
1611906357
VCH2020
HANA git-
mergetime
29.01.2021 08:45
VCH2020
HANA hdb-state
RAMP
VCH2020
HANA makeid
8370882
VCH2020
HANA rev-
changelist
1611906357
VCH2020
HANA rev-
patchlevel
0
VCH2020
HANA sapexe-
branch
753_REL
VCH2020
HANA sapexe-
changelist
2007209
VCH2020
HANA sapexe-
version
753
VCH2020
HANA sp-
patchlevel
0
VCH2020
PPMS-SP-Level
2054
VCH2020
PPMS-SP-Patch-
Level
0
VCH2020
PPMS-Technical-
Name
SAPVCHAFL2020
VCH2020
PPMS-Technical-
Release
2020
VCH2020
afl-state
RAMP
VCH2020
changeinfo
CONT
f83110dc622dccaf20fa0d8127995d1a01e2d364
(fa/afls42020sp05_rel)
VCH2020
compilebranch
fa/afls42020sp05_rel
VCH2020
compiler-version
GCC 9
VCH2020
compiler-version-
full
gcc (SAP release 20200227, based on SUSE gcc9-
9.2.1+r275327-1.3.7) 9.2.1 20190903 [gcc-9-branch
revision 275330]
VCH2020
compiletype
rel

39
Plug-in
Key
Value
VCH2020
component-key
vch2020
VCH2020
compversion-id
7,35549E+19
VCH2020
date
29.01.2021 15:10
VCH2020
fullversion
202.005.400.001.611.000.000
VCH2020
git-hash
f83110dc622dccaf20fa0d8127995d1a01e2d364
VCH2020
git-headcount
28
VCH2020
git-mergeepoch
1611929286
VCH2020
git-mergetime
29.01.2021 15:08
VCH2020
keycaption
SAP VCH AFL 2020
VCH2020
keyname
SAPVCHAFL2020
VCH2020
keyvendor
sap.com
VCH2020
makeid
8372591
VCH2020
online-installation-
plugin
yes_with_restart
VCH2020
online-upgrade-
plugin
1
VCH2020
platform
linuxx86_64
VCH2020
release
2020
VCH2020
required-
components
name="HDB"; vendor="sap.com";
version="[2.00.054.00.1611906357,2.00.054.00.1611
906357]"
VCH2020
rev-changelist
1611929286
VCH2020
rev-number
54
VCH2020
rev-patchlevel
0
VCH2020
server-plugin
1
VCH2020
sp-number
2054
VCH2020
sp-patchlevel
0
VCH2020
vch-version
2020.28.0 (2020.07.07)
Plug-in
Key
Value
AFL
HANA auxversion
0000.00.0
6.1.3 SAP NetWeaver 7.50 application server JAVA with Adobe
Document Services installed
Product Name
Name
Version
Vendor
Description
SAP NETWAVER
J2EE
7.50
16
sap.com
SAP NETWEAVER 7.5: Adobe Document Services
SAP NETWAVER
J2EE
7.50
16
sap.com
SAP NETWEAVER 7.5: Application Server Java

40
6.1.4 Windows Remote Desktop
o SAP GUI for Windows 7.60
o SAP HANA Studio & ABAP Development Tools (2020-12)
o SAP Lumira 2.4 (Discovery & Designer)
o Google Chrome
o Mozilla Firefox
6.1.5 SAP BusinessObjects BI Platform 4.2
o SBOP BI PLATFORM 4.2 SP07 SERVER LINUX (64B)
o SAP Lumira Server for BI Platform

www.sap.com/contactsap
© 2021 SAP SE or an SAP affiliate company. All rights reserved.
No part of this publication may be reproduced or transmitted in any
form or for any purpose without the express permission of SAP SE
or an SAP affiliate company.
The information contained herein may be changed without prior
notice. Some software products marketed by SAP SE and its
distributors contain proprietary software components of other
software vendors. National product specifications may vary.
These materials are provided by SAP SE or an SAP affiliate company
for informational purposes only, without representation or warranty
of any kind, and SAP or its affiliated companies shall not be liable for
errors or omissions with respect to the materials. The only
warranties for SAP or SAP affiliate company products and services
are those that are set forth in the express warranty statements
accompanying such products and services, if any. Nothing herein
should be construed as constituting an additional warranty.
SAP and other SAP products and services mentioned herein as well
as their respective logos are trademarks or registered trademarks of
SAP SE (or an SAP affiliate company) in Germany and other
countries. All other product and service names mentioned are the
trademarks of their respective companies. Please see
www.sap.com/corporate-en/legal/copyright/index.epx for
additional trademark information and notices.